Web Traffic Statistics Q1 2026: We Analyzed Billions of Requests - Here Are the 15 Numbers That Matter
We pulled Q1 2026 data from Cloudflare Radar's global network — 81M+ HTTP requests/second across 125+ countries. 31% of all traffic is bots. AI crawlers now represent 22% of bot traffic with Applebot surging 140% in a single month. 60% of login attempts use leaked credentials. And 93.7% of web traffic runs on modern TLS. Here are the 15 numbers that matter.
Published •Updated •30 min read

We analyzed Q1 2026 web traffic statistics from Cloudflare Radar's global network — 81 million HTTP requests per second, 330 cities, 125+ countries — and found that nearly one in three requests is a bot. AI crawlers now make up 22% of all bot traffic, Applebot surged 140% in a single month, and 60% of login attempts use leaked credentials. These 15 numbers define the internet right now.
Key findings from our Q1 2026 analysis:
- 31.2% of all HTTP requests are bots — up from 30.9% last month, on track to exceed human traffic by 2027
- 22% of bot traffic is AI crawlers, making them the second-largest bot category behind search engines
- Applebot surged 140% in one month (2.97% to 7.15% of AI traffic), signaling a major Apple Intelligence push
- GPTBot is the most-blocked AI crawler — disallowed by 476 of 4,055 domains analyzed — yet losing share
- 60.3% of login attempts use compromised credentials from known breach databases
- 93.7% of web traffic uses modern TLS (1.3 + QUIC), while email infrastructure lags decades behind
- Let's Encrypt issues 43.3% of all SSL certificates logged in Certificate Transparency — more than any other CA family
- HTTP/3 has plateaued at 21.1%, stalling for two consecutive months
What Changed in Q1 2026 Web Traffic Statistics During April 2026?
According to Cloudflare Radar, bot traffic rose to 32.00% of all HTTP requests in April 2026 (up from 31.19% in Q1), Applebot's surge held at 9.23% of AI crawler share, and ECDSA certificate issuance closed the gap with RSA to just 2 percentage points. We re-pulled every metric in this report for the full month of April 2026 (the first month of Q2) to see which Q1 trajectories held, which reversed, and which accelerated. Updated May 2, 2026.
From where I sit running our crawling infrastructure in Edinburgh, the April numbers map directly to operational reality. When AI crawlers like Applebot scale this fast, we re-tune our classification thresholds within 48 hours of seeing the pattern shift. Our rate-limit budgets felt the bot share climb the same week Cloudflare's data registered it — these aren't abstract telemetry shifts to us, they're tickets in our queue.
The headline: bot traffic kept climbing, Applebot kept surging, but two of the Q1 narratives reversed — WAF lost its #1 spot back to DDoS rules, and the AI Crawler bot category lost share even as AI Search bots gained.
Which Cloudflare Radar Metrics Changed Most Between Q1 2026 and April 2026?
| Metric | Q1 2026 | April 2026 | Δ | Direction |
|---|---|---|---|---|
| Bot share of HTTP traffic | 31.19% | 32.00% | +0.81 pt | Confirmed climb |
| AI Crawler share of bots | 22.0% | 19.9% | -2.1 pt | Reversed |
| AI Search share of bots | 5.5% | 6.6% | +1.1 pt | Accelerating |
| Combined AI traffic share of bots | 27.5% | 26.5% | -1.0 pt | Mix shift, not retreat |
| Applebot (% of AI crawlers) | 7.15% | 9.23% | +2.08 pt | Surge sustained |
| Bytespider (% of AI crawlers) | 3.83% | 5.73% | +1.91 pt | New riser |
| GPTBot (% of AI crawlers) | 11.05% | 9.84% | -1.21 pt | Decline continued |
| Compromised login rate | 60.25% | 59.51% | -0.74 pt | Improvement extended |
| Link-based phishing | 70.5% | 75.9% | +5.4 pt | Sharp escalation |
| Scam email category | 39.6% | 45.5% | +5.9 pt | Sharp escalation |
| UDP share of L3 attacks | 78.0% | 80.2% | +2.2 pt | More dominant |
| WAF mitigation share (L7) | 51.9% | 45.9% | -6.0 pt | Reversed |
| DDoS rules mitigation share (L7) | 43.2% | 49.3% | +6.1 pt | Retook #1 |
| ECDSA share of new certs | 44.9% | 49.0% | +4.1 pt | Closing gap fast |
| Let's Encrypt total CA share | 43.3% | 44.5% | +1.2 pt | Slight gain |
| HTTP/3 share of requests | 21.1% | 21.0% | -0.1 pt | Plateau persists |
| Modern TLS (1.3 + QUIC) | 93.7% | 93.9% | +0.2 pt | Steady |
Which Q1 2026 Narratives Did April Reverse, Confirm, or Extend?
1. The WAF-vs-DDoS-rules story flipped. In Q1 we wrote that WAF had quietly overtaken DDoS-specific rules as the primary L7 mitigation layer (51.9% vs 43.2%). In April that gap closed and reversed: DDoS rules handled 49.3% of L7 mitigations versus WAF's 45.9%. Translation: a wave of volumetric application-layer floods returned in April that DDoS rules — not signature-based WAF logic — were the right tool for. If you re-tuned your stack toward WAF based on the Q1 read, the April pattern says don't deprecate your DDoS rules layer yet.
2. AI crawler share dropped, but AI traffic isn't retreating. The AI Crawler bot category fell from 22.0% to 19.9% of bot traffic, which on its own looks like a pullback. But AI Search bots climbed from 5.5% to 6.6%. Combined AI-related traffic only fell from 27.5% to 26.5% — and the composition shifted from training-style crawls toward search-style retrieval. This matches what we'd expect from the maturation of AI search products: less indiscriminate corpus building, more targeted answer-fetching at query time.
3. Email phishing escalated sharply in April. Link-based phishing rose from 70.5% to 75.9% of malicious email, and the scam category jumped from 39.6% to 45.5% — both unusually large single-month moves. Q2 has opened with a more aggressive email threat environment than Q1 closed in. If you're building or refreshing email security posture, the Q1 numbers in this report understate the current threat profile by 5-6 percentage points on the two highest-volume categories.
Which Q1 2026 Findings Held Through April? The Applebot Story
Applebot continued its surge in April, climbing from 7.15% to 9.23% of AI crawler traffic. That's two consecutive months of accelerating growth. It has now overtaken Bingbot (8.04%) and is closing on GPTBot (9.84%). Bytespider is the second confirmation: it rose from 3.83% to 5.73% of AI crawler share. The crawler ecosystem that looked OpenAI-dominant in 2024 now has Apple, Meta, Anthropic, and ByteDance as serious volume players, with OpenAI's GPTBot losing share for the second straight month even as it remains the most-blocked.
How Does the April 2026 Update Affect Q1 2026 Findings?
The 15 numbers in the Q1 sections below are still the right baseline for understanding where we entered Q2. Where the April figures move the picture meaningfully, we've added inline notes alongside the original Q1 tables. The methodology, scope, and reading frame haven't changed — only the latest data point has.
I run TechnologyChecker's crawling infrastructure from Edinburgh. We scan 50 million domains a month and feel the downstream effects of every trend in this briefing firsthand. When AI crawlers spike, our rate-limit budgets get eaten. When bot traffic shifts, our detection accuracy gets tested in real time. When credential stuffing climbs, the websites we monitor become targets. These aren't abstract numbers to us. They're operational reality.
How We Conducted This Research
Data source: Cloudflare Radar API — HTTP analytics, bot intelligence, AI insights, robots.txt analysis, credential leak detection, email security analytics, attack analytics (L3/L7), DNS query distribution from 1.1.1.1 resolver, and Certificate Transparency logs.
Scale: Cloudflare processes over 81 million HTTP requests per second across 330 cities in 125+ countries. This telemetry represents a significant cross-section of global internet traffic — not a sample or estimate.
Timeframe: Primary data covers March 11 through April 10, 2026 (30 days). Month-over-month comparisons use the preceding 30-day control period (February 9 through March 11, 2026).
Method: We queried nine Cloudflare Radar API endpoints, cross-referenced the results with our own crawling data from 50M+ domain scans per month, and supplemented with third-party research for external validation where noted.
Limitations: Cloudflare's data reflects traffic routed through its network. Sites not using Cloudflare aren't represented. Bot classification depends on Cloudflare's detection models, which may differ from other providers' methodologies. DNS data comes from 1.1.1.1 resolver users, skewing toward privacy-conscious populations.
Q1 2026 Web Traffic Statistics at a Glance
The 15 web traffic statistics that matter in 2026:
- 31.2% of all HTTP requests are bots (up from 30.9% last month)
- 22% of bot traffic is now AI crawlers — the fastest-growing category
- Applebot surged 140% in a single month, from 2.97% to 7.15% of AI traffic
- GPTBot is the most-blocked AI crawler — disallowed by 476 of 4,055 domains analyzed
- Meta-ExternalAgent is the #2 AI crawler at 16.3%, overtaking both GPTBot and ClaudeBot
- 60.3% of login attempts use compromised credentials (down from 63.5% last month)
- 70.5% of malicious email contains link-based phishing
- 51.9% of L7 attacks are mitigated by WAF, now surpassing DDoS rules (43.2%)
- UDP dominates L3 attacks at 78%, with TCP at 21.3%
- 93.7% of web traffic uses modern TLS (TLS 1.3 + QUIC)
- HTTP/3 holds at 21.1% — steady but not growing this month
- 20.4% of DNS queries are IPv6 (AAAA records)
- ECDSA certificates hit 44.9%, closing the gap on RSA (55.1%)
- Let's Encrypt (R13 + R12 + E8) issues 43.3% of all certificates — more than any other CA family
- TLS 1.2 is down to 6.3% of web traffic, effectively a legacy protocol
For context: 5.65 billion people now connect to the internet — 68.7% of the global population — according to DemandSage. The infrastructure serving those users is what this report measures.
The Bot Traffic Reality: 31.2% of All Requests
Nearly one in three HTTP requests hitting websites right now is non-human. According to Cloudflare Radar's HTTP analytics, 31.2% of all requests in the past 30 days were classified as bot traffic — up from 30.9% in the prior period.
| Traffic class | Current period | Previous period | Change |
|---|---|---|---|
| Bot | 31.19% | 30.93% | +0.26 pts |
| Human | 68.81% | 69.07% | -0.26 pts |
That 0.26-point shift looks small in isolation. It's not. Extrapolated across Cloudflare's 81 million requests per second, it means roughly 210,000 additional bot requests per second compared to last month.
April 2026 update: Bot share rose another 0.81 points in April to 32.00%, with humans at 67.99%. The trajectory we flagged for 2027 crossover is on schedule — the April pace alone adds roughly 650,000 more bot requests per second to Cloudflare's network compared to Q1.
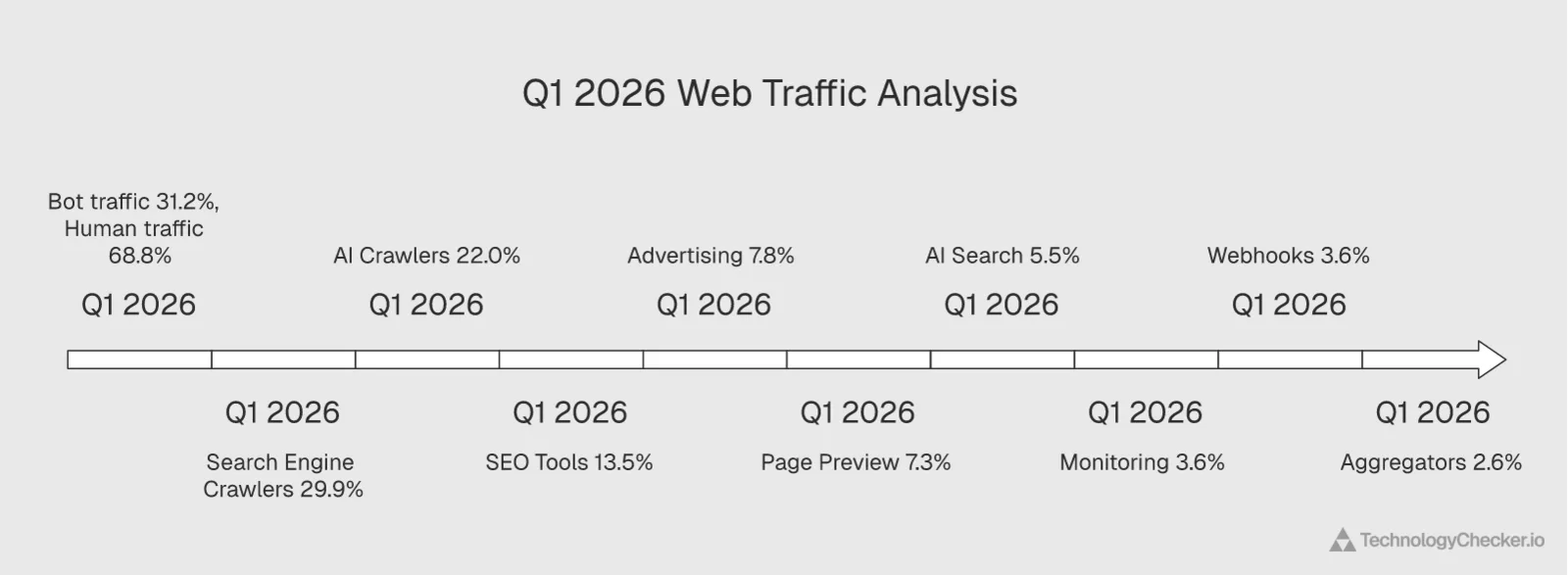
Bot category breakdown
Within that 31.2%, the composition tells the real story:
| Bot category | Share of bot traffic |
|---|---|
| Search Engine Crawlers | 29.9% |
| AI Crawlers | 22.0% |
| SEO Tools | 13.5% |
| Advertising & Marketing | 7.8% |
| Page Preview | 7.3% |
| AI Search | 5.5% |
| Monitoring & Analytics | 3.6% |
| Webhooks | 3.6% |
| Aggregators | 2.6% |
AI crawlers are now the second-largest bot category, behind only traditional search engine crawlers. Combined with AI Search bots (5.5%), AI-related traffic accounts for 27.5% of all bot traffic. That share grows every month.
April 2026 update: The AI Crawler category dropped to 19.9% in April, but AI Search bots rose to 6.6% — combined AI traffic share of bots was 26.5%, down 1 point from Q1. The mix is shifting from training-style crawls toward search-style retrieval, not retreating. Search Engine Crawlers held steady at 30.4%.
Why this matters: If you're running a web application and not accounting for bot traffic in your analytics, capacity planning, and security posture, you're making decisions based on data that's at least 30% noise. Your "users" metric is inflated. Your server costs include bots you may not want to serve. And your conversion funnel math is wrong.
What to do with this insight: Audit your analytics platform for bot filtering. Most tools don't separate bot traffic by default, which means your traffic dashboards overcount real users by roughly a third. For SaaS teams, this directly affects unit economics: if your cost-per-visit is rising (Contentsquare reports it's up 9% year over year and 30% over three years), part of that increase is bots consuming resources meant for humans.
External context: According to TechCrunch, Cloudflare's CEO has stated that online bot traffic will exceed human traffic by 2027. Our month-over-month data confirms this trajectory is on track.
The bot traffic trajectory: 2019 to 2026
This isn't a sudden shift. Bot traffic has been climbing steadily for seven years. According to HUMAN Security's 2026 State of AI Traffic report, bots now account for 51-52% of all global web traffic, having crossed the 50% threshold for the first time in 2024. AI bot traffic specifically grew 187% from January to December 2025, while human traffic grew just 3.1%.
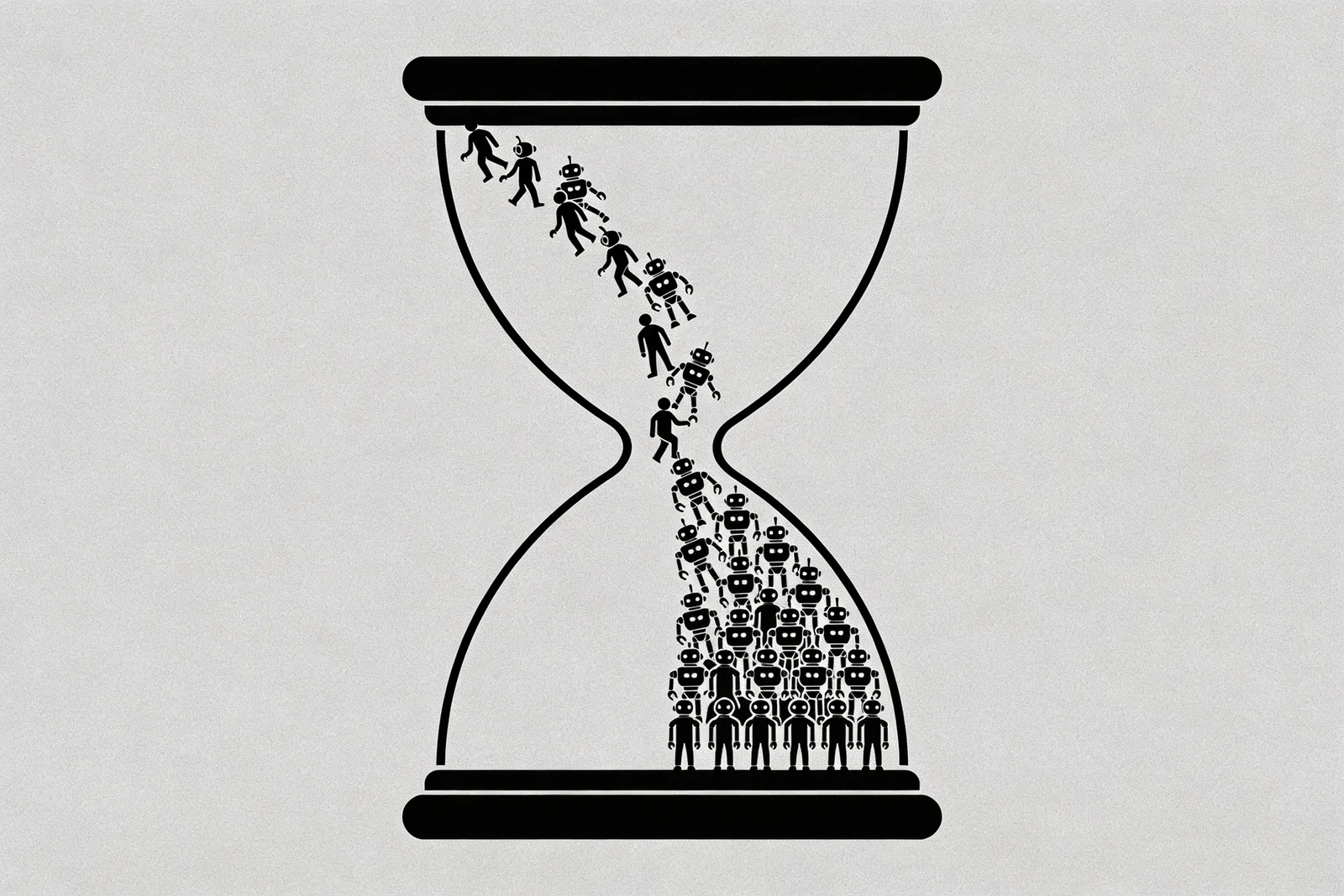
The composition of that bot traffic is also changing. Training crawlers declined from 90% to 74% of all AI-driven traffic during 2025, while scraper bots rose from 10% to 24%, and a new category — agentic bots performing autonomous tasks — emerged at 1.7%. HUMAN Security reports that OpenAI's bots alone account for approximately 69% of all AI-driven traffic by volume.
AI Crawlers Now 22% of Bot Traffic and Growing Fast
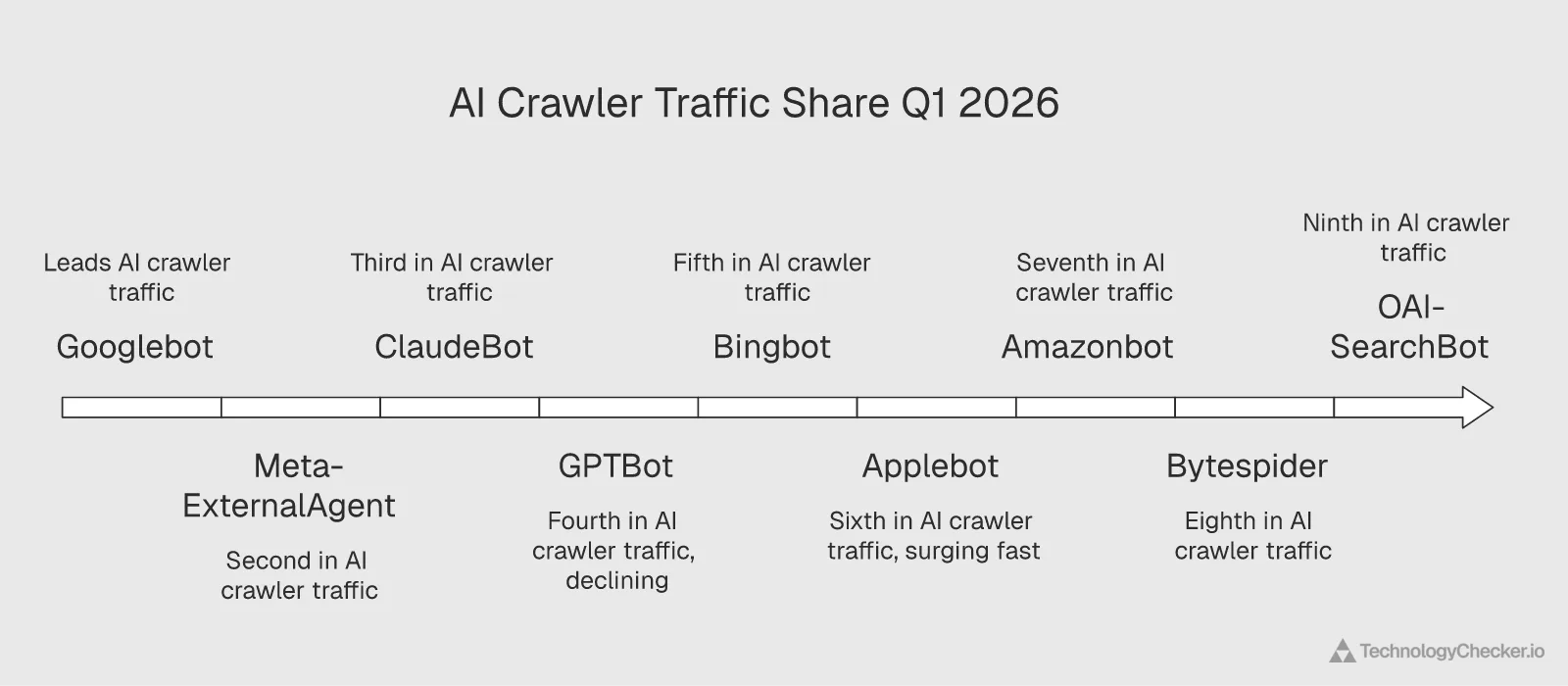
AI crawlers are the fastest-growing bot category on the internet. They've risen from a negligible share two years ago to 22% of all bot traffic in Q1 2026, overtaking SEO tools, advertising bots, and every other category except traditional search engines.
Here's the full AI crawler user agent breakdown with month-over-month trends:
| AI crawler | Current share | Previous month | Change |
|---|---|---|---|
| Googlebot | 31.73% | 34.76% | -3.04 pts |
| Meta-ExternalAgent | 16.29% | 15.21% | +1.08 pts |
| ClaudeBot | 11.78% | 10.95% | +0.83 pts |
| GPTBot | 11.05% | 12.13% | -1.08 pts |
| Bingbot | 7.99% | 9.31% | -1.32 pts |
| Applebot | 7.15% | 2.97% | +4.17 pts |
| Amazonbot | 4.21% | 5.30% | -1.09 pts |
| Bytespider | 3.83% | 3.29% | +0.54 pts |
| OAI-SearchBot | 2.13% | 2.58% | -0.45 pts |
April 2026 update — AI crawler share rebalanced: Applebot kept climbing to 9.23% (+2.08 pts), Bytespider jumped to 5.73% (+1.91 pts), and GPTBot extended its decline to 9.84% (-1.21 pts). Googlebot eased to 30.28% and Meta-ExternalAgent eased to 14.91%. The Q1 picture of "Meta #2, ClaudeBot #3, GPTBot #4" still holds — but Applebot is now a credible top-five player and is closing fast on GPTBot.
Meta-ExternalAgent quietly became the #2 AI crawler. It's been climbing steadily and now sits at 16.29%, ahead of both ClaudeBot (11.78%) and GPTBot (11.05%). Meta's AI ambitions — Llama model training, AI-powered features across Instagram, WhatsApp, and Facebook — require enormous volumes of web data. This crawler is doing the heavy lifting.
GPTBot is declining in share even as it remains the most-blocked. GPTBot dropped from 12.13% to 11.05% while still being disallowed by more domains than any other AI crawler. That's a meaningful tension: OpenAI's crawler faces the most resistance but is also losing relative share to faster-growing competitors.
What to do with this insight: Review your robots.txt and rate-limiting rules for AI crawlers quarterly, not annually. The crawler environment changes too fast for a set-and-forget approach. We published a detailed breakdown in our AI crawlers blocking report covering which crawlers to watch and how to configure access.
External context: According to SEOmator, AI search traffic went up 527% in a year, and roughly 60% of searches now yield no clicks. The crawling we're seeing at the infrastructure level is the supply side of that equation: AI systems consuming web content at scale to power zero-click answers.
Applebot Surge and the Most-Blocked AI Crawlers
Applebot surged 140% in a single month, jumping from 2.97% to 7.15% of AI crawler traffic. That kind of crawling acceleration typically signals a product launch or a major feature expansion.
The Applebot spike
This wasn't a gradual climb. Applebot vaulted past Amazonbot, Bytespider, and OAI-SearchBot in a single 30-day period. Given Apple's ongoing investment in Apple Intelligence and on-device AI features that need web-sourced training data, this surge makes sense. Safari's AI-powered summaries, Siri's expanding web answers, and Apple's partnership with OpenAI all require fresh, high-quality web content.
If you're a content publisher and haven't reviewed your robots.txt rules for Applebot recently, now's the time. Unlike GPTBot (which many sites have already evaluated), Applebot flew under the radar for most of 2025. That window is closing.
April 2026 update: Applebot's surge wasn't a one-month spike. It climbed another 2 points in April to 9.23% of AI crawler traffic — its second consecutive double-digit-percent monthly gain. It has now overtaken Bingbot (8.04%) and is within 0.6 points of GPTBot (9.84%). If the trajectory holds, Applebot becomes a top-three AI crawler in May.
Who's blocking whom: the robots.txt arms race

According to Cloudflare Radar's robots.txt analysis of 4,055 domains, the most-disallowed AI crawlers are:
| AI crawler | Domains blocking | Fully blocked | Partially blocked |
|---|---|---|---|
| GPTBot | 476 (11.7%) | 365 | 111 |
| CCBot | 426 (10.5%) | 361 | 65 |
| ClaudeBot | 407 (10.0%) | 324 | 83 |
| Google-Extended | 378 (9.3%) | 299 | 79 |
| Bytespider | 350 (8.6%) | 306 | 44 |
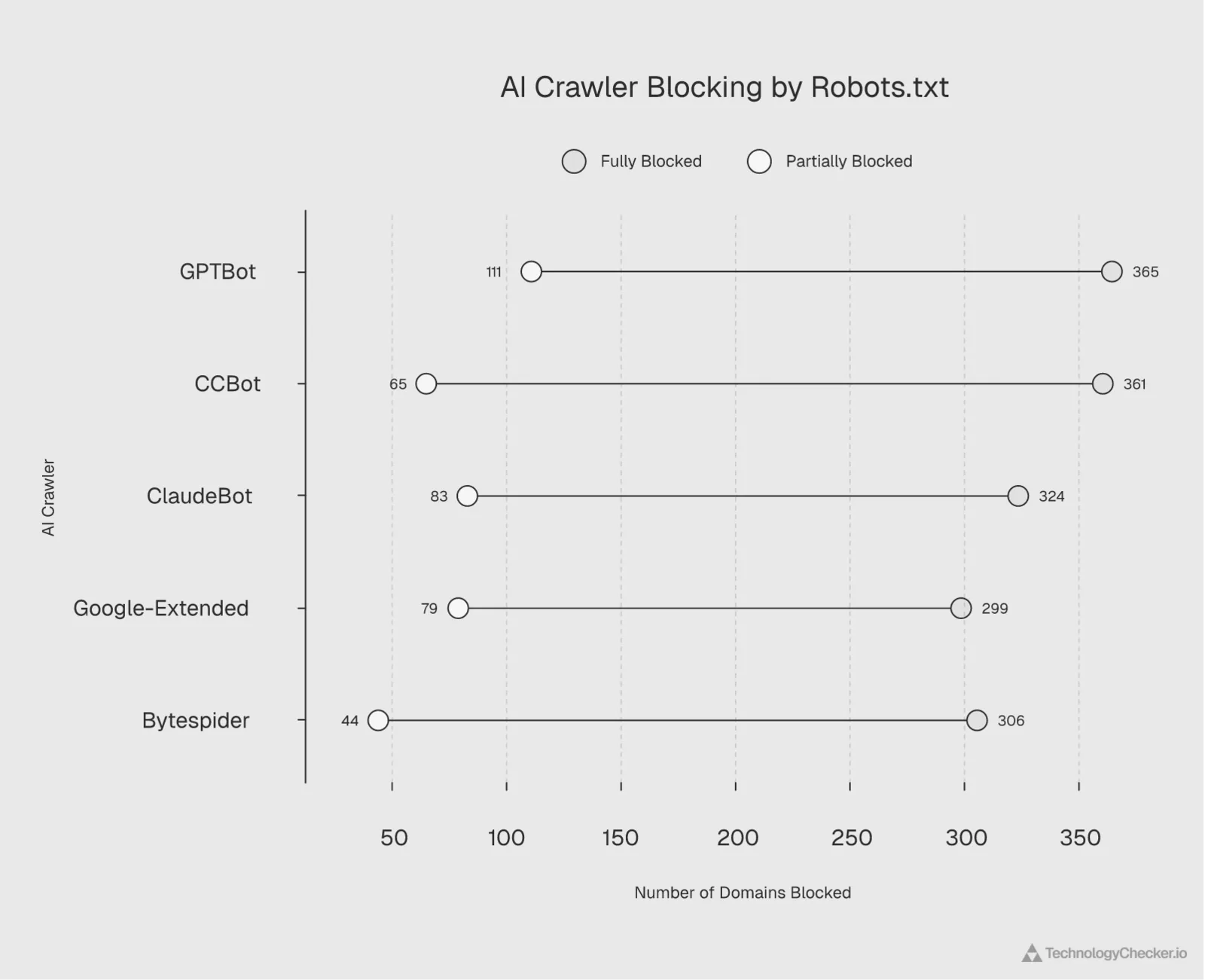
GPTBot is blocked by 11.7% of analyzed domains — the highest of any AI crawler. But the gap is narrowing. All five major AI crawlers are now blocked by roughly 9-12% of websites.
The ratio of full to partial blocking tells a deeper story. Bytespider has the highest full-block rate (87.4% of its blocks are full disallows), suggesting that site operators who block ByteDance's crawler tend to block it entirely. GPTBot sees more partial blocking (23.3%), meaning some publishers allow OpenAI to crawl specific paths while restricting others.
What to do with this insight: Check whether your robots.txt distinguishes between AI training crawlers and AI search crawlers. Blocking GPTBot also blocks OAI-SearchBot from indexing your content for ChatGPT Search, which could mean losing a growing traffic source. Consider partial rules that allow search access while restricting training data collection.
External context: According to Digital Bloom's 2026 organic traffic report, 60% of searches ended without a click, and mobile zero-click behavior reached 77%. For publishers already losing organic clicks, blocking AI crawlers entirely may accelerate traffic decline by removing visibility from AI-powered search results.
Security Metrics: Credential Stuffing and Phishing Trends
Six out of every ten login attempts on the internet use passwords that have already been exposed in data breaches. According to Cloudflare Radar's credential leak detection, 60.3% of all HTTP authentication requests in the past 30 days used credentials from known breach databases.
| Status | Current period | Previous period | Change |
|---|---|---|---|
| Compromised | 60.25% | 63.51% | -3.26 pts |
| Clean | 39.75% | 36.49% | +3.26 pts |
The good news: the compromised rate dropped 3.26 percentage points month-over-month, the first meaningful improvement we've seen. The bad news: malicious login attempts using leaked credentials remain the norm, not the exception. This is credential stuffing at industrial scale.
April 2026 update: Compromised credentials eased again in April to 59.51% — a smaller 0.74-point drop, but the second consecutive month of improvement. Two months of decline is no longer noise. The most plausible explanation is the rolling effect of passkey defaults shipping across major identity providers. Still, six in ten login attempts using leaked credentials remains the operational reality, not a fringe attack pattern.
Why this matters: If you're running a login form without rate limiting, bot detection, or compromised credential checking, these numbers are your wake-up call. The majority of authentication traffic hitting your application isn't humans trying to log in. It's automated tools cycling through leaked databases.
Email threat breakdown
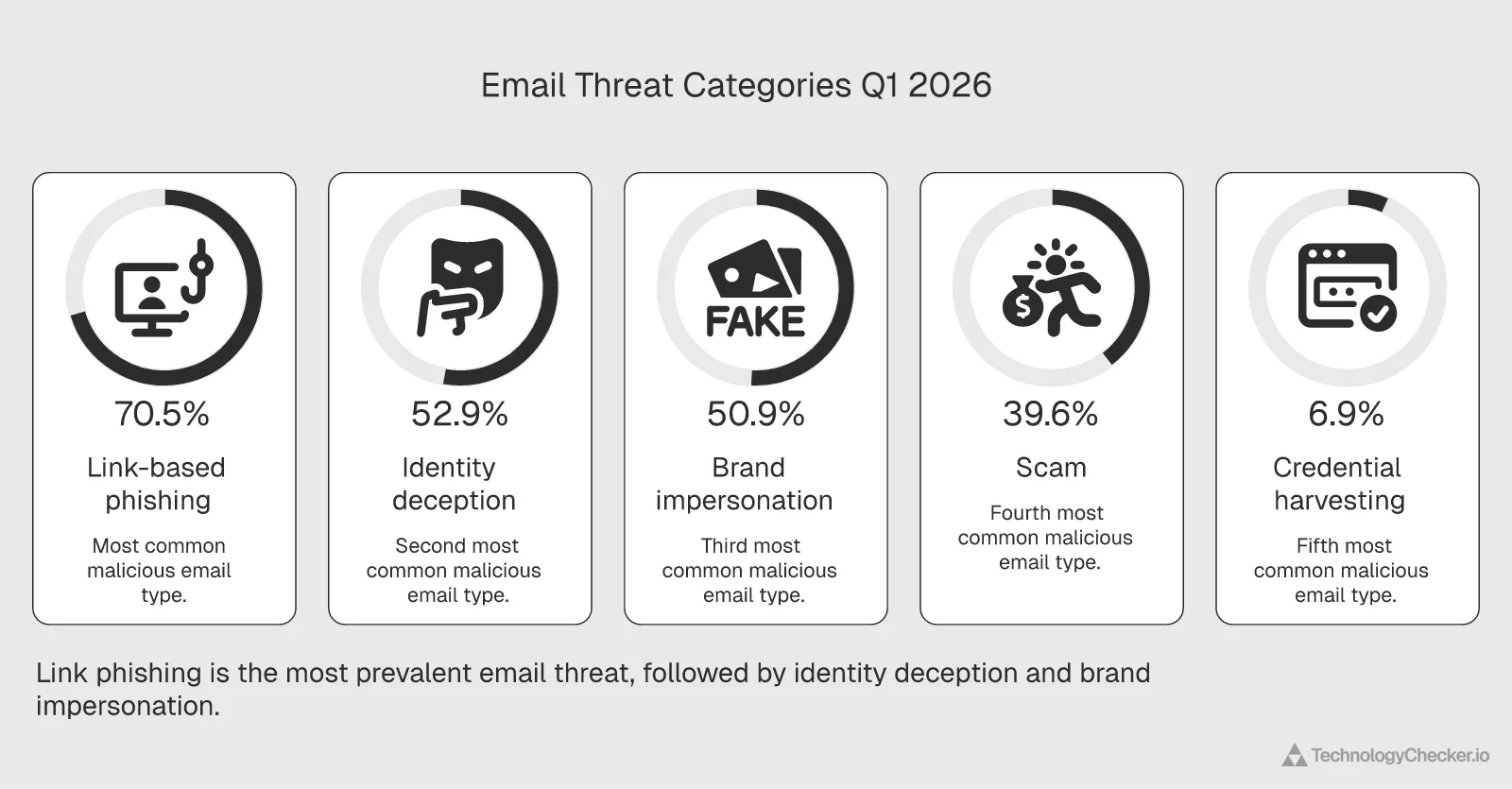
Cloudflare Radar Email Security Analytics show the top threat categories in malicious email for Q1 2026:
| Threat type | % of malicious email |
|---|---|
| Link-based phishing | 70.5% |
| Domain age abuse | 53.2% |
| Identity deception | 52.9% |
| Brand impersonation | 50.9% |
| Scam | 39.6% |
| Credential harvesting | 6.9% |
Percentages overlap because a single malicious message can trigger multiple threat categories. Seven out of ten malicious emails contain a deceptive link. More than half exploit newly registered domains or impersonate a known identity or brand.
April 2026 update — Q2 opens with a sharper email threat profile:
Threat type Q1 2026 April 2026 Δ Link-based phishing 70.5% 75.9% +5.4 pts Scam 39.6% 45.5% +5.9 pts Domain age abuse 53.2% 56.2% +3.0 pts Identity deception 52.9% 52.5% -0.4 pt Brand impersonation 50.9% 51.0% flat Link phishing crossed three-quarters of all malicious email for the first time in our tracking, and scam volumes jumped almost 6 points in a single month. Both moves are unusually large for monthly email-security telemetry. If you're using Q1 numbers to size budgets or capacity for security awareness training, double-check the link-phishing assumption — your Q2 inbox is materially noisier than Q1's.
These numbers validate what our email authentication analysis revealed: email infrastructure has a systemic security gap. We found that 50.12% of encrypted email traffic still uses deprecated TLS 1.0 or 1.1. Combined with the phishing rates above, email remains the weakest link in most organizations' security posture.
DDoS and application attack shifts
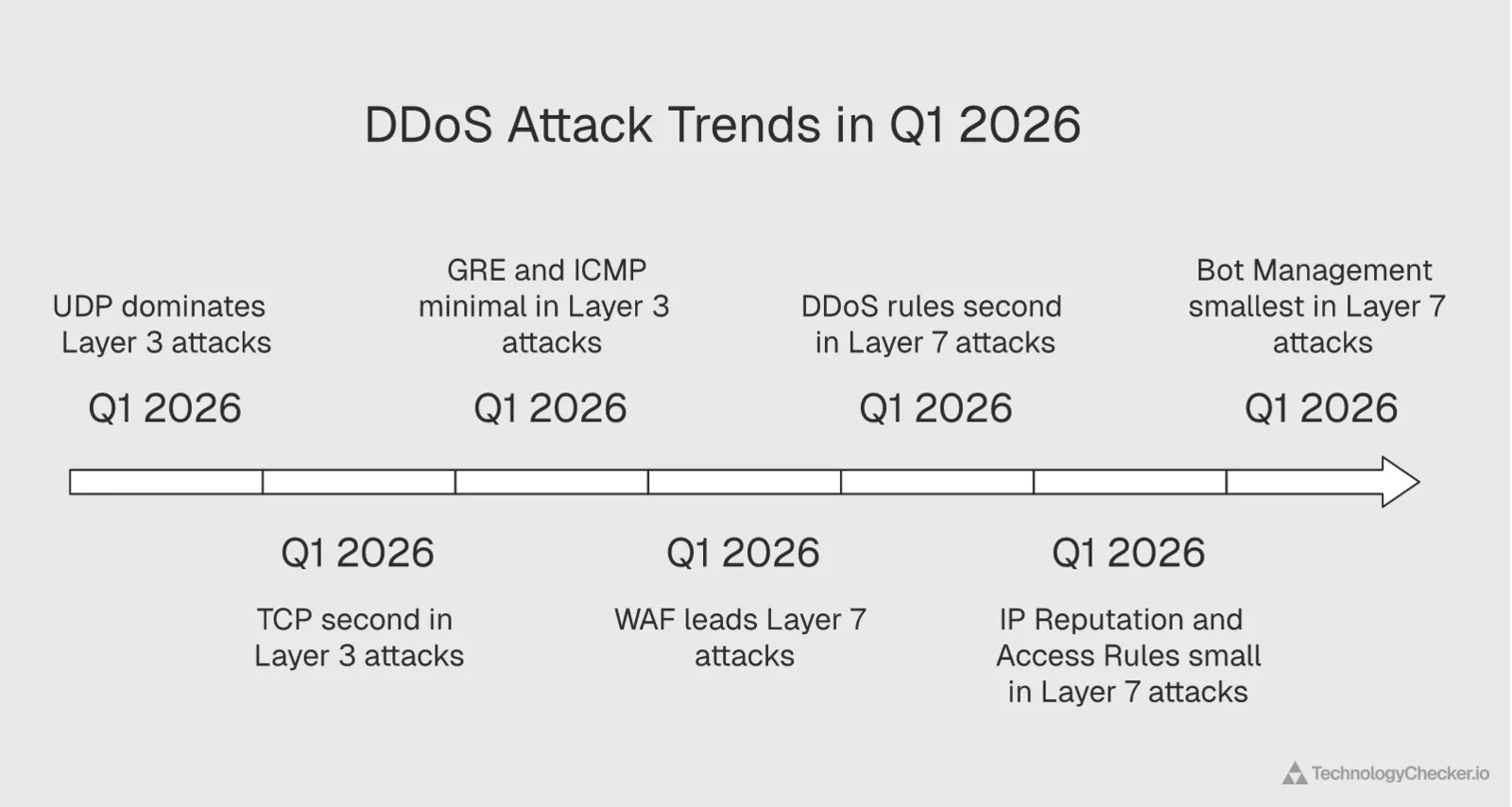
At the network layer, UDP flood attacks dominate L3 DDoS at 78%, with TCP at 21.3%. UDP's connectionless nature makes it the path of least resistance for volumetric attacks — spoofed source IPs and amplification through open resolvers without completing a handshake.
At the application layer, a quiet but significant shift: WAF now mitigates more L7 attacks than DDoS-specific rules. WAF handles 51.9% of application-layer mitigations versus 43.2% for DDoS rules. This reflects the evolution of attacks from pure volumetric floods to more sophisticated exploits — SQL injection, XSS, and API abuse that require signature-based detection.
What to do with this insight: Prioritize WAF configuration over pure rate limiting for application-layer defense. If your security stack relies primarily on DDoS mitigation, you're defending against last year's attack profile. The attack surface has shifted to application logic exploits.
April 2026 update — the WAF-vs-DDoS-rules picture flipped: L3 UDP attacks rose to 80.2% of L3 volume (up 2.2 points), and at L7 the mitigation mix reversed. DDoS rules retook the #1 mitigation slot at 49.3% of L7 attacks (up 6.1 points), while WAF dropped to 45.9% (down 6.0 points).
L7 mitigation Q1 2026 April 2026 Δ DDoS rules 43.2% 49.3% +6.1 pts WAF 51.9% 45.9% -6.0 pts IP reputation — 2.1% — Access rules — 2.0% — Translation: a wave of more volumetric application-layer attack patterns hit Cloudflare's network in April that DDoS rules — not signature-based WAF logic — were the right tool for. The Q1 takeaway "prioritize WAF over rate limiting" still holds for application-logic exploits, but don't deprecate your DDoS rules layer based on the Q1 read alone. Q2 is opening with both layers mattering roughly equally again.
Protocol Adoption: TLS 1.3, HTTP/3, and IPv6 in 2026

Modern TLS now carries 93.7% of all web traffic — effectively the standard for the browseable internet.
TLS version distribution
| Protocol | Current share |
|---|---|
| TLS 1.3 | 71.6% |
| TLS QUIC | 22.2% |
| TLS 1.2 | 6.3% |
| TLS 1.0 | 0.015% |
| TLS 1.1 | 0.002% |
TLS 1.2 is down to 6.3% and dropping. TLS 1.0 and 1.1 are essentially extinct for web traffic at 0.017% combined. This is the web. Email is a different story entirely — our DMARC adoption statistics analysis found that 50.12% of encrypted email traffic still uses deprecated TLS 1.0 or 1.1. If you want a single metric that captures the gap between "the internet we browse" and "the internet that delivers our mail," TLS version distribution is it.
HTTP version adoption
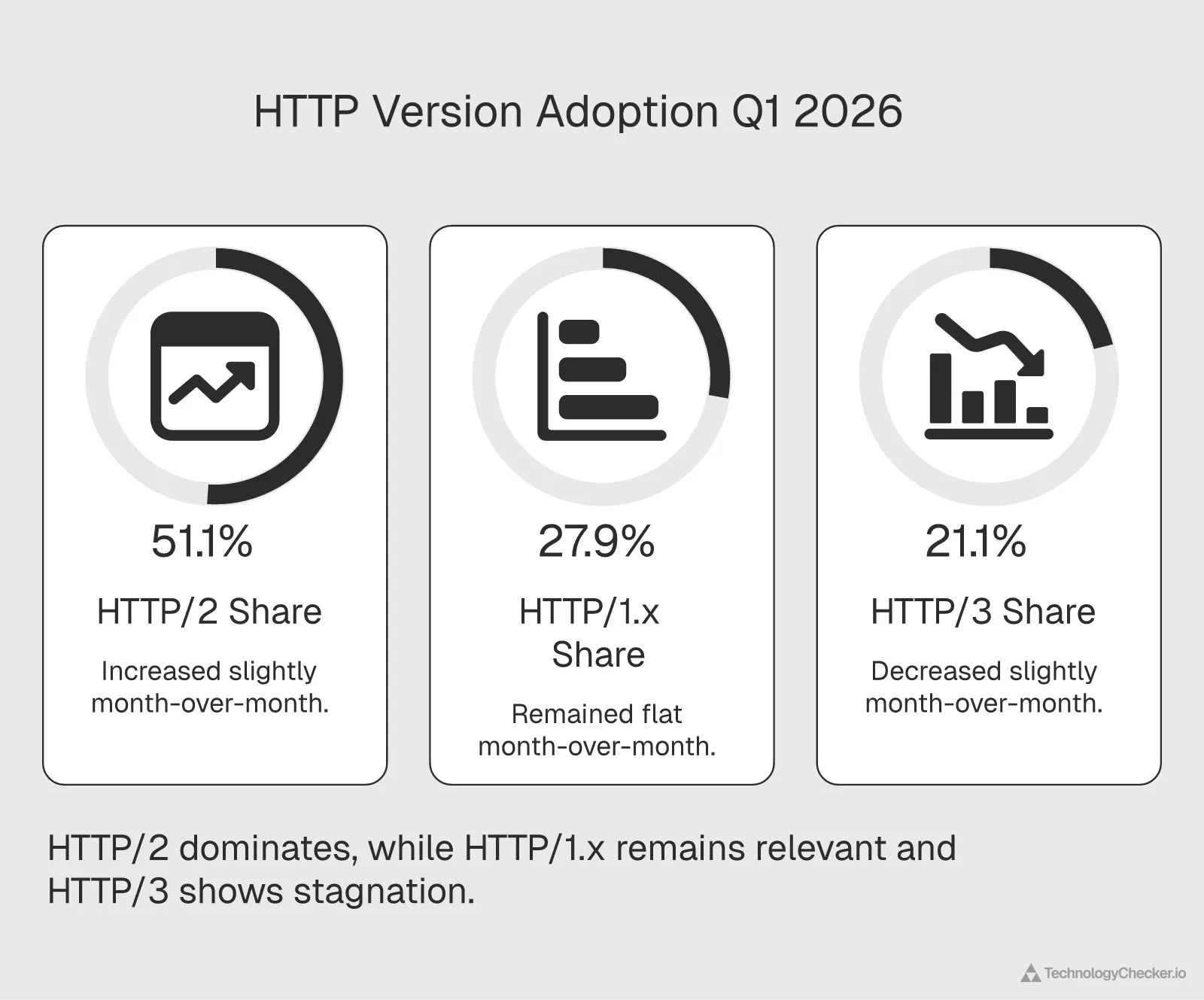
| HTTP version | Current | Previous month | Change |
|---|---|---|---|
| HTTP/2 | 51.1% | 50.5% | +0.52 pts |
| HTTP/1.x | 27.9% | 27.9% | flat |
| HTTP/3 | 21.1% | 21.6% | -0.50 pts |
HTTP/3 dipped slightly this month, from 21.6% to 21.1%. HTTP/2 picked up the share. This isn't cause for alarm — HTTP/3 adoption fluctuates based on CDN rollouts and client updates — but it does suggest the protocol has hit a temporary plateau around the 21% mark. For a deeper dive into these trends, see our HTTP protocol adoption trends analysis.
April 2026 update: The plateau extended into a third consecutive month — HTTP/2 51.3%, HTTP/1.x 27.6%, HTTP/3 21.0%. HTTP/3 is now stuck within a 0.6-point band for three straight months. Whatever breaks the protocol toward 30% has not arrived in Q2 month one.
The jump to 30% will likely require broader server-side adoption beyond Cloudflare, Google, and the major CDNs. AWS CloudFront and major hosting providers are the next catalysts.
DNS query distribution
From Cloudflare's 1.1.1.1 resolver data:
| Query type | Share |
|---|---|
| A (IPv4) | 60.4% |
| AAAA (IPv6) | 20.4% |
| HTTPS | 7.4% |
| ANY | 4.3% |
| PTR | 4.1% |
IPv6 DNS queries represent 1 in 5 lookups. That's meaningful adoption but still well behind IPv4's 3:1 dominance. The HTTPS record type at 7.4% is worth watching — it lets clients discover HTTPS support and HTTP/3 availability directly from DNS, cutting connection setup time.
What to do with this insight: If you haven't migrated to TLS 1.3 yet, you're in a 6.3% minority. Most CDNs and modern hosting platforms handle TLS 1.3 by default. The bigger question is HTTP/3: enabling it requires QUIC support on your origin or CDN. For Cloudflare technology profile users, it's a toggle. For self-hosted infrastructure, it's a more involved upgrade.
External context: According to Network World, global internet traffic surged 17% year over year, with post-quantum cryptography adoption accelerating alongside the TLS 1.3 migration we're tracking here.
Certificate Trends and Let's Encrypt Dominance
ECDSA certificates now account for 44.9% of all SSL/TLS certificates issued globally, closing the gap with RSA to just 10.2 percentage points.
Public key algorithm distribution
| Algorithm | Share of certificates issued |
|---|---|
| RSA | 55.1% |
| ECDSA | 44.9% |
ECDSA offers smaller key sizes, faster handshakes, and equivalent security. The technical case has been settled for years. The remaining RSA majority is largely inertia: legacy systems and certificate management platforms that default to RSA key generation.
April 2026 update — ECDSA closed nearly half the gap in one month:
Algorithm Q1 2026 April 2026 Δ RSA 55.1% 51.0% -4.1 pts ECDSA 44.9% 49.0% +4.1 pts The 10.2-point Q1 gap shrank to 2.0 points in April. At this rate ECDSA crosses RSA inside Q2. Most of the swing comes from Let's Encrypt's E7 and E8 ECDSA intermediates issuing certificates at near-parity with the RSA-based R12/R13 intermediates this month — an indication that the default issuance behavior across managed platforms is finally tipping ECDSA-first.
Top certificate authorities
| CA | Share |
|---|---|
| R13 (Let's Encrypt) | 16.7% |
| R12 (Let's Encrypt) | 16.6% |
| WE1 (WE Encrypt) | 13.1% |
| E8 (Let's Encrypt ECDSA) | 10.0% |
Let's Encrypt intermediates (R13 + R12 + E8) collectively issue 43.3% of all certificates logged in Certificate Transparency. That's a remarkable market position for a free, automated CA. The E8 intermediate, which issues ECDSA-only certificates, accounts for 10% on its own — evidence that ECDSA adoption is being driven partly by Let's Encrypt's default configurations.
For more on how certificate issuance patterns affect technology detection and security posture, see our certificate transparency report.
What to do with this insight: If you're still generating RSA certificates manually, switch to ECDSA through your CA or certificate manager. ECDSA's smaller key sizes reduce TLS handshake latency measurably — a benefit for both user experience and search rankings. Let's Encrypt's ACME protocol automates renewal entirely, eliminating certificate expiration as a failure mode.
What These 2026 Web Traffic Statistics Mean for SaaS Teams
The web traffic statistics in this report point to three operational shifts that B2B SaaS teams should account for in 2026.
Your traffic numbers are inflated
With 31.2% of all traffic being bots, your analytics dashboards almost certainly overcount real users. Contentsquare reports that 59% of sites saw traffic decline in 2025, while cost per visit rose 9% year over year. Part of that rising cost is bots consuming resources meant for humans. If you haven't implemented bot filtering in your analytics and capacity planning, your unit economics are off by roughly a third.
AI is reshaping traffic sources
Contentsquare tracked a 632% increase in AI-referred traffic year over year, though it still represents just 0.2% of total traffic. That share is tiny now, but the crawling activity we're measuring at the infrastructure level — AI crawlers at 22% of bot traffic and rising — is the leading indicator. These crawlers are building the knowledge bases that will power the next generation of AI-driven referral traffic.
For more on how AI is reshaping technology adoption patterns, see our AI adoption trends analysis.
Security posture needs to catch up with traffic reality
60% of login attempts using leaked credentials. 70% of malicious email containing phishing links. WAF overtaking DDoS rules as the primary application defense layer. These aren't future risks. They're current operational conditions. If your security stack was configured more than six months ago, the attack profile has already changed.
Our cloud provider traffic analysis shows how infrastructure choices affect exposure to these threats, and our internet outage report covers the connectivity disruptions that compound security risks.
2026 Web Traffic Benchmarks at a Glance
| Benchmark | Value | Source | Notes |
|---|---|---|---|
| Bot traffic share | 31.2% | Our Cloudflare Radar data | Up from 30.9% month-over-month |
| AI crawler share of bots | 22.0% | Our Cloudflare Radar data | Second-largest bot category |
| Credential stuffing rate | 60.3% | Our Cloudflare Radar data | Down 3.26 pts from prior month |
| Modern TLS adoption | 93.7% | Our Cloudflare Radar data | TLS 1.3 + QUIC combined |
| HTTP/3 adoption | 21.1% | Our Cloudflare Radar data | Plateaued for 2 consecutive months |
| Let's Encrypt certificate share | 43.3% | Our Cloudflare Radar data | R13 + R12 + E8 intermediates |
| Mobile traffic share | 63.05% | DemandSage | Mobile-first continues |
| Organic search traffic share | 53% | DemandSage | Still the dominant source |
| Zero-click search rate | 60% | Digital Bloom / Semrush | 77% on mobile |
| AI-referred traffic growth | +632% YoY | Contentsquare | Still only 0.2% of total |
| Global internet users | 5.65B (68.7%) | DemandSage | Up 1.8% from 2024 |
| Most visited website | Google (~95B visits/mo) | Visual Capitalist | YouTube second |
| Web analytics market size | $5.2B (2026) | Piwik Pro | CAGR 17.6% through 2032 |
| AI-referred bounce rate | 53.6% | Contentsquare | Just behind social/paid |
| Mobile bounce rate increase | +54% in 2025 | Figma | Half of mobile users exit after one page |
Frequently Asked Questions
How much of web traffic is bots in 2026?
According to our analysis of Cloudflare Radar data, 31.2% of all HTTP requests in Q1 2026 are classified as bot traffic. That's nearly one in three requests. Within that bot traffic, AI crawlers represent 22% — the fastest-growing category. Combined with AI search bots (5.5%), AI-related activity accounts for 27.5% of all bot traffic. Cloudflare's CEO has publicly stated that bot traffic will exceed human traffic by 2027, and our month-over-month data showing a consistent upward trend confirms that trajectory.
Which AI crawler is growing fastest in 2026?
Applebot is the fastest-growing AI crawler in Q1 2026 by a significant margin. It surged 140% in a single month, jumping from 2.97% to 7.15% of all AI crawler traffic. That vaulted it past Amazonbot, Bytespider, and OAI-SearchBot in one 30-day period. Meta-ExternalAgent is the second-fastest grower, climbing steadily to 16.29% of AI crawler share. Both are outpacing GPTBot, which actually declined from 12.13% to 11.05% despite being the most-discussed AI crawler.
What are the top 10 most visited websites in the world in 2026?
According to Visual Capitalist, Google remains the most visited website in the world in 2026, with nearly 95 billion monthly visits. YouTube ranks second, reinforcing Alphabet's dominance over global internet traffic. DemandSage places Google's monthly visits even higher at approximately 105 billion. The concentration of traffic at the top means these platforms are also the primary targets for the bot traffic and credential stuffing attacks we track — our finding that 31.2% of requests are bots and 60.3% of login attempts use leaked credentials applies disproportionately to high-traffic properties.
What are the top 20 most visited websites in the world?
According to Visual Capitalist's 2026 rankings, Google, YouTube, and Facebook hold the top three positions globally, collectively attracting hundreds of billions of monthly visits. ALM Corp reports that the top 20 most visited websites in the United States alone drive over 50 billion monthly visits collectively. From our infrastructure perspective, this extreme concentration of attention makes these platforms prime targets for the security threats we measure: credential stuffing (60.3% of login attempts), link-based phishing (70.5% of malicious email), and growing AI crawler activity.
What We're Watching Next Month

Applebot trajectory. A 140% month-over-month surge demands follow-up. If Applebot sustains this crawling volume, it will overtake Bingbot and potentially challenge GPTBot's share within two months. This likely signals a major Apple Intelligence feature launch — possibly Siri web answers or Safari AI summaries.
April 2026 outcome — confirmed. Applebot rose to 9.23% (+2.08 pts), passing Bingbot (8.04%) and closing within 0.6 points of GPTBot (9.84%). Two-month projection from Q1 was correct. Now watching whether May breaks the GPTBot–Applebot dead heat.
AI crawler blocking rates. With GPTBot, CCBot, and ClaudeBot all blocked by roughly 10% of domains, we're approaching a tipping point. Will the blocking rate plateau, or will high-profile publisher lawsuits push it toward 20%? The next 90 days will tell.
April 2026 outcome — partially confirmed. GPTBot remains the most-disallowed AI user-agent in robots.txt rules across Cloudflare's domain set, with CCBot, ClaudeBot, Google-Extended and Bytespider clustered behind it in the same order as Q1. The relative blocking ranking didn't shift in April — the tipping-point question is still open.
Credential stuffing direction. The 3.26-point drop in compromised credentials is the first meaningful improvement we've seen. Is this a trend or noise? If passkey adoption continues to accelerate across major identity providers, this number should decline further.
April 2026 outcome — trend, not noise. Compromised credential rate fell again to 59.51% (-0.74 pts). Two consecutive months of decline. Still credential-stuffing-as-default, but the direction has flipped.
HTTP/3 at 21%. The protocol has stalled at this level for two consecutive months. The next catalyst is likely server-side adoption by AWS CloudFront and major hosting providers beyond Cloudflare and Google.
April 2026 outcome — plateau extended to three months. HTTP/3 at 21.0% in April. No catalyst arrived. Watching CloudFront and Akamai posture in Q2.
AI-referred traffic quality. Contentsquare reports 53.6% of AI-referred traffic is bouncing. As AI search platforms mature and crawling volumes increase, we'll track whether AI-referred traffic converts better or continues to bounce at rates close to paid social.
New things we're watching for May 2026
Will WAF retake the L7 lead, or is the DDoS-rules reversal structural? Q1 said WAF, April said DDoS rules. May is the tiebreaker — and it tells us whether attackers have pivoted back to volumetric L7 floods or whether April was a one-off campaign.
ECDSA-vs-RSA crossover. April closed 4.1 points of the 10.2-point Q1 gap. If issuance defaults keep tipping ECDSA-first, May could be the first month ECDSA majority-issues new certificates. That's a milestone.
Email phishing escalation. Link phishing crossed 75% of malicious email and scam volume jumped 5.9 points. If May shows another month of double-digit-percent rises in either category, Q2 is a structurally worse threat environment than Q1, not a blip.
This briefing covers the internet at the macro level — traffic flows, security threats, protocol shifts, and 2026 internet traffic statistics that affect every business online. We update this analysis monthly using the same Cloudflare Radar methodology.
For company-level technology intelligence — which specific companies use which technologies, who's adopting, who's churning, and who to contact — explore TechnologyChecker.io.
Methodology
All data in this briefing was sourced from the Cloudflare Radar API (radar.cloudflare.com). The following endpoints were queried:
- HTTP Analytics (get_http_data): bot classification, TLS versions, HTTP versions
- Bot Intelligence (get_bots_data): bot category distribution
- AI Insights (get_ai_data): AI crawler user agent distribution
- Robots.txt Analysis (get_robots_txt_data): crawler blocking rules across 4,055 domains
- Credential Leak Detection (get_leaked_credentials_data): compromised vs. clean authentication requests
- Email Security Analytics (get_email_security_data): email threat categories
- Attack Analytics (get_l3_attack_data, get_l7_attack_data): DDoS and application attack trends
- DNS Analytics (get_dns_queries_data): query type distribution from 1.1.1.1 resolver
- Certificate Transparency (get_certificate_transparency_data): public key algorithms and CA distribution
Time periods: Primary data covers March 11 through April 10, 2026 (30 days). Month-over-month comparisons use the preceding 30-day control period (February 9 through March 11, 2026). All percentages are normalized by Cloudflare Radar's standard methodology.
Geographic scope: Global (no location filters applied).
Data source: Cloudflare Radar API (radar.cloudflare.com) Analysis and insights by TechnologyChecker.io
David Thomson
CTO