DMARC adoption statistics 2026: 89% of emails pass DMARC but 14.5% still fail SPF
We pulled 90 days of Q1 2026 email security data from Cloudflare Radar and cross-referenced it against Valimail, Red Sift, the Verizon DBIR, and the FBI IC3 report. DMARC pass rates hit 88.99%, but only 42% of domains actually enforce it. SPF jumped 6 points YoY to 80.24%, BEC losses hit $2.77B, and 27.61% of email still uses deprecated TLS 1.0. Here's what the numbers say about email authentication maturity.
Published •Updated •28 min read
We pulled 90 days of Cloudflare Radar email security data for Q1 2026. DMARC pass rates now sit at 88.99% globally, up from 86.42% a year earlier. SPF enforcement jumped nearly six percentage points over the same window. Those are the headline numbers, and they're good.
Then I kept reading. 27.61% of email traffic is still negotiating TLS 1.0, a transport protocol the IETF formally deprecated in March 2021. Five years ago. That was the finding that stopped me cold.
Key findings from our Q1 2026 email authentication analysis:
- DMARC pass rate hit 88.99% globally in Q1 2026, up from 86.42% in Q1 2025 (+2.58 points YoY).
- SPF had the biggest jump of any protocol, climbing from 74.27% to 80.24%. That's a +5.97 point swing in twelve months, driven by post-enforcement compliance after the Google and Yahoo bulk sender mandate.
- DKIM quietly leads the pack at 90.90% pass rate, with the lowest fail rate of any authentication method (1.67%).
- 14.54% of all emails still fail SPF, even though DMARC is widely enforced. That's the authentication gap every deliverability team is fighting.
- 91.79% of emails now travel encrypted in transit, up from 89.67% a year ago. But 1 in 12 still flows in plaintext.
- TLS 1.0 accounts for 27.61% of email transport. Combined with TLS 1.1 (22.51%), more than half of encrypted email is using protocols deprecated five years ago.
- 18.11% of all inbound emails are spoof attempts. Roughly 1 in every 5.5 messages arriving at a Cloudflare-protected mailbox.
- 70.07% of emails have no ARC header, so most forwarded mail loses its original authentication chain.
How Did Email Authentication and TLS Security Evolve in April 2026?
According to Cloudflare Radar email security, DMARC pass rates reached 89.48% in April 2026 (up 0.49 points), SPF pass rates climbed to 81.62% (up 1.38 points), but deprecated TLS 1.0 share grew to 29.89% — pushing combined deprecated TLS (1.0 + 1.1) past 51.65% of encrypted email transport. We re-pulled every Cloudflare Radar email-security dimension for the full month of April 2026. The post's central deprecated-TLS finding got worse, not better. Updated May 2, 2026.
The deprecated-TLS getting worse despite DMARC and SPF improving isn't a contradiction — it's exactly what I'd expect from running scanning infrastructure across 50 million domains. The long tail of senders being pulled into "encrypted" transport in April is overwhelmingly older MTA software with hardcoded TLS 1.0 defaults. We see this exact pattern in our own crawler logs every time small-business email volume scales up: the encrypt-in-transit headline rate climbs while the actual cipher quality flatlines. That's the gap I'd want every email security buyer to read into the April numbers — encryption-in-transit is becoming a misleading proxy without the TLS-version breakdown.
How Did Email Security Metrics Shift Between Q1 2026 and April 2026?
| Metric | Q1 2026 (post) | April 2026 | Δ | Direction |
|---|---|---|---|---|
| DMARC pass rate | 88.99% | 89.48% | +0.49 pt | Continued improvement |
| DMARC fail rate | 4.33% | 5.55% | +1.22 pt | Slightly worse |
| DMARC none rate | 6.68% | 4.97% | -1.71 pt | More domains publishing |
| SPF pass rate | 80.24% | 81.62% | +1.38 pt | Continued improvement |
| SPF fail rate | 14.54% | 14.67% | +0.13 pt | Flat |
| SPF none rate | 5.23% | 3.71% | -1.52 pt | More domains publishing |
| DKIM pass rate | 90.90% | 90.41% | -0.49 pt | Slightly down |
| DKIM fail rate | 1.67% | 2.13% | +0.46 pt | Slightly up |
| TLS 1.0 share | 27.61% | 29.89% | +2.28 pt | Got worse |
| TLS 1.1 share | 22.51% | 21.76% | -0.75 pt | Slightly down |
| TLS 1.2 share | (Q1 not cited) | 18.03% | new | Stable |
| TLS 1.3 share | (Q1 not cited) | 30.32% | new | Modern fraction |
| Combined deprecated TLS (1.0 + 1.1) | 50.12% | 51.65% | +1.53 pt | Worsening |
| Spoof rate | 18.11% | 24.33% | +6.22 pt | Sharp escalation |
| Spam rate | (Q1 not cited) | 4.65% | new baseline | — |
| Malicious email rate | (Q1 not cited) | 19.57% | new baseline | — |
Which Q1 2026 Narratives Did April Reverse, Confirm, or Extend?
1. Authentication is improving — but TLS in transit is getting worse, not better. Q1's central uncomfortable finding was that 50.12% of email TLS still uses 1.0 or 1.1, protocols deprecated by the IETF in March 2021. April's data extends the bad news: TLS 1.0 grew by 2.28 points to 29.89%, and the combined deprecated bucket rose to 51.65%. While DMARC, SPF, and the encrypt-in-transit headline rate keep climbing, the quality of that encryption is moving the wrong way. Most plausible explanation: the long-tail of senders pushed onto encrypted transport by Q1's improvements is using legacy MTA software that defaults to TLS 1.0/1.1. The "encryption-in-transit" metric is becoming a misleading proxy for transport security if you read it without the version breakdown.
2. Spoof attempts surged 6 points in a single month. Q1 measured 18.11% of inbound emails as spoof attempts (1 in every 5.5 messages). April measured 24.33% — 1 in every 4.1 messages. That's a +6.22-point single-month escalation. This aligns with what we saw in our web-traffic-statistics refresh, where link-phishing rose 5.4 pts and scam categories rose 5.9 pts in April. The Q2 email threat environment is structurally more aggressive than Q1's. If you used the post's Q1 spoof rate to size detection or budget, that figure now understates by ~6 points.
3. The DMARC enforcement gap closed slightly — domains are publishing more. DMARC "NONE" (no policy published) fell from 6.68% to 4.97% in April; SPF NONE fell from 5.23% to 3.71%. Both shifts indicate the long tail of holdouts is finally publishing records. The Google/Yahoo enforcement effect (the Q1 post's central explanation for the 5.97-pt YoY SPF jump) is still rippling out 14 months after the February 2024 deadline. The remaining laggards aren't bulk senders — they're small operators and legacy systems being pulled in by deliverability pressure.
Which Q1 2026 Email Authentication Patterns Held Through April?
DKIM continued to lead all three protocols at 90.41% pass rate, narrowly down from Q1's 90.90% — the "DKIM quietly does the heavy lifting" Q1 read remains correct. SPF's structural fail rate held essentially flat at 14.67%; the multi-hop alignment problem isn't being solved, it's being papered over by DMARC's "either-SPF-or-DKIM" pass logic.
April produced 19.57% malicious and 4.65% spam classification rates as new Q2 baselines. We didn't have these as Q1 cite-able numbers, so we'll track them month-over-month from May onward.
What Should We Watch for in May 2026?
Will the deprecated TLS share keep growing? A second consecutive month of TLS 1.0 expansion would confirm a structural problem: the legacy MTA cohort being pulled into "encryption" without modernizing their TLS stack. If May shows TLS 1.0 above 30%, the Q1 post's "five years deprecated and still 27.61%" framing badly understates the issue.
Spoof rate trajectory. A jump from 18% to 24% in a single month is unusual. May tells us if the April escalation is sustained (and the threat environment has structurally worsened) or a one-month spike from a specific campaign cycle.
The DMARC enforcement gap. With domains-without-DMARC down to 4.97%, the next milestone is sub-4%. Watching whether the long tail of small senders keeps publishing or whether we've hit the floor of permanent-non-adopters.
Every email authentication decision a company makes leaves a trail in the DNS and in the message headers. Adding a DMARC record. Enforcing p=reject. Rotating DKIM keys. Upgrading TLS versions. Each of those actions writes a public fingerprint that anyone on the internet can read. We can't see inside your marketing stack, but we can see whether your engineering team bothered to secure the front door.
I spent five years on the Search team at Google working on large-scale crawling and indexing systems. One of the lessons I took away from that period: DNS records are the internet's version of a company's LinkedIn profile. They're public, they're structured, and they reveal more than people think they do. A company that publishes no DMARC record has told you something about itself, whether it meant to or not.
I run TechnologyChecker's crawling infrastructure now from Edinburgh. We scan 50 million domains a month and we see DMARC, SPF, and DKIM records every single day. But DNS records only tell you what a company claims to support. They don't tell you whether the actual mail flow passes verification when it arrives at a recipient. For that, you need network-level data. So we pulled Q1 2026 email security telemetry from Cloudflare Radar, which aggregates patterns from the billions of messages processed by Cloudflare Email Security each quarter. Then we cross-referenced it against the industry's most cited third-party datasets from Valimail, Red Sift, and the Verizon 2025 Data Breach Investigations Report.
Here's what the combined data says, what it means for your deliverability, and why email authentication maturity is one of the most reliable technology sophistication signals we've ever measured.
The global numbers for Q1 2026
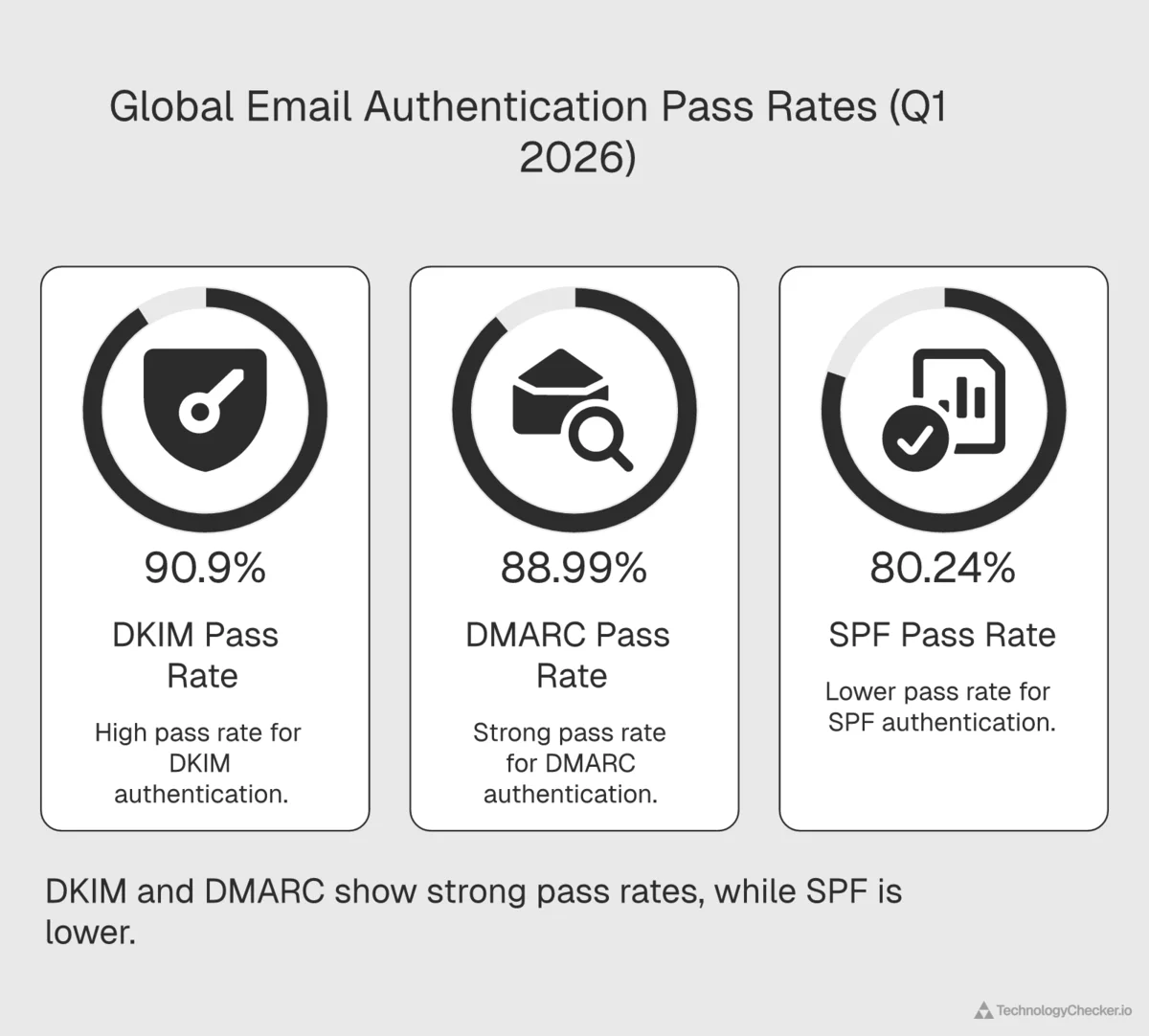
Here are the headline numbers from Cloudflare Radar for the full Q1 2026 period (January 1 through March 31, 2026):
| Protocol | PASS | FAIL | NONE | What "NONE" means |
|---|---|---|---|---|
| DMARC | 88.99% | 4.33% | 6.68% | No DMARC policy published |
| SPF | 80.24% | 14.54% | 5.23% | No SPF record published |
| DKIM | 90.90% | 1.67% | 7.43% | Message not signed with DKIM |
A few patterns jump out.
DKIM has the highest pass rate of any authentication method, beating DMARC by nearly 2 percentage points and SPF by more than 10. That's counterintuitive. Most people assume DMARC is the "strictest" protocol because it's the enforcement layer, but DMARC only passes if either SPF or DKIM passes with alignment. In practice, DKIM is doing most of the heavy lifting worldwide.
SPF fails 14.54% of the time. That's more than 3x the DMARC fail rate and nearly 9x the DKIM fail rate. SPF has a well-known structural weakness: every hop, every forwarding server, every mailing list relay can break its alignment. The numbers confirm what deliverability engineers have been saying for a decade. SPF alone is not enough, and relying on it for authentication is fragile.
And 6.68% of emails still arrive from domains with no DMARC policy at all. One in every 15 messages. Google and Yahoo have required DMARC from bulk senders since February 1, 2024, with the requirements announced jointly on October 3, 2023. The remaining long tail is either very small senders, legacy infrastructure, or organizations that simply haven't caught up.
The enforcement gap: why Cloudflare's 89% and Valimail's 42% both tell the truth
If you spend any time reading DMARC research, you'll run into an apparent contradiction. Cloudflare says 88.99% of emails pass DMARC. Valimail's 2026 State of DMARC Report says only 42% of domains with DMARC records are actually in enforcement (p=reject or p=quarantine), leaving a 36-point gap between awareness (78%) and real protection. Valimail's finding sounds catastrophic. Cloudflare's sounds rosy. Both are right. They measure different things.
Cloudflare's 88.99% is a message-weighted pass rate. It counts the share of actual emails arriving at Cloudflare-protected mailboxes that pass DMARC evaluation. The number is dominated by high-volume senders (Google Workspace, Microsoft 365, SendGrid, Mailgun, and the big transactional providers) which have had DMARC perfectly configured for years. So when you look at the volume of mail, authentication is mature.
Valimail's 42% is a domain-weighted enforcement rate. It counts the share of DMARC-publishing domains that have set p=reject or p=quarantine. This one captures the long tail: millions of small and mid-sized companies that published a DMARC record (often because Google or Yahoo told them to) but left it at p=none, which provides monitoring and zero actual blocking. From a security posture standpoint, those domains are wide open to spoofing even though they technically "have DMARC."
In practical terms: the big senders you receive mail from are doing fine. The domains you might impersonate (competitors, suppliers, acquisition targets) are mostly not. Both realities matter, depending on whether you're thinking about your inbound security or your outbound deliverability.
Valimail's report notes that enforcement grew from 35% to 42% over the course of 2025. That's a 7-point improvement. But the report also concludes that "most domains with DMARC are not fully protected" and that the enforcement gap "represents a growing sentiment of organizations that have implemented DMARC to meet basic mailbox provider requirements but remain entirely unprotected against domain spoofing and AI-driven impersonation." That's the ceiling any mandate can hit. Google and Yahoo can force you to publish a record. They can't force you to actually enforce it.
Year-over-year: The biggest SPF jump we've ever measured
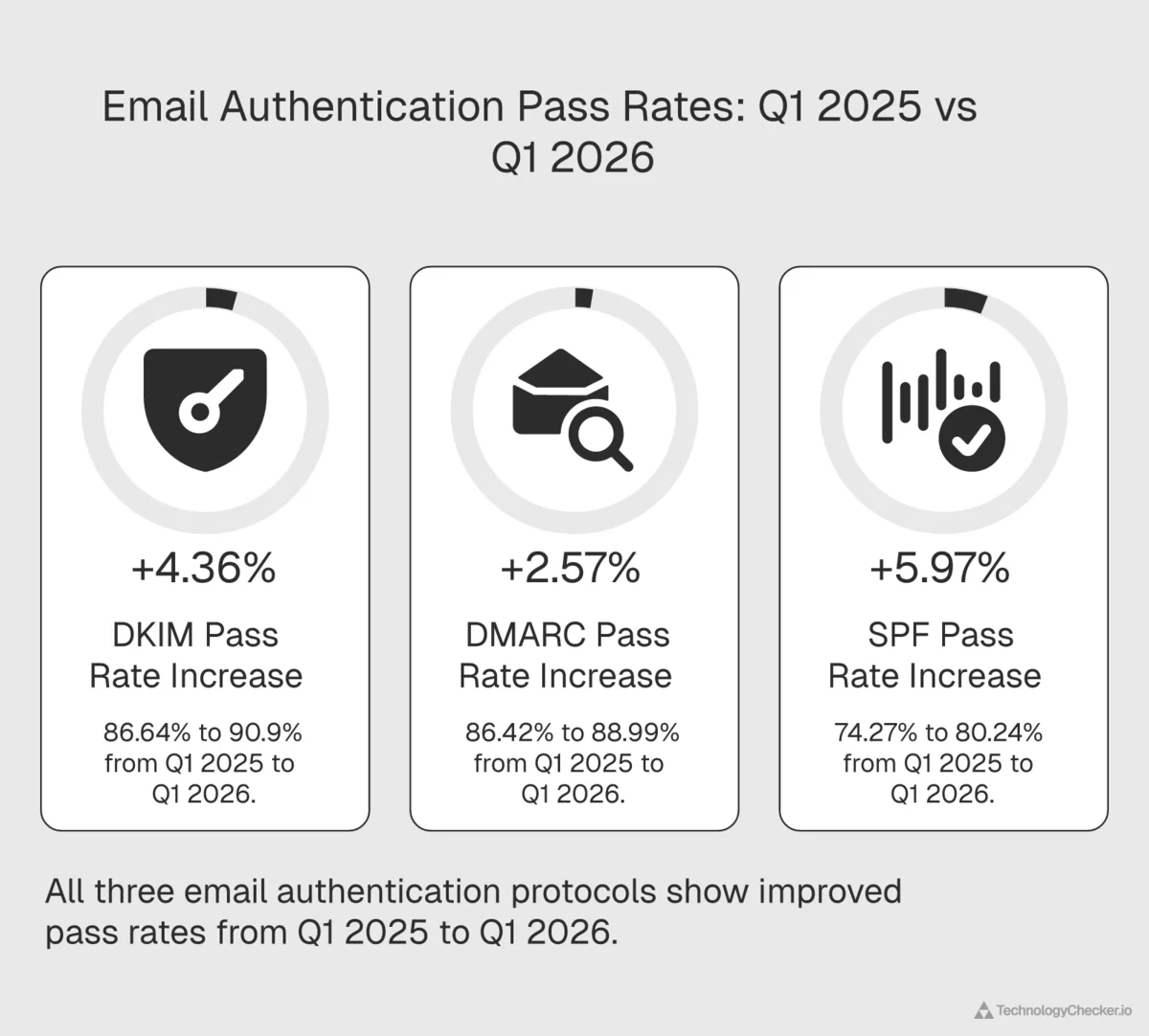
To understand how fast email authentication is maturing, we pulled the same Q1 summary for 2025 and compared it directly:
| Metric | Q1 2025 | Q1 2026 | YoY Delta |
|---|---|---|---|
| DMARC PASS | 86.42% | 88.99% | +2.58 pts |
| DMARC FAIL | 5.79% | 4.33% | −1.46 pts |
| SPF PASS | 74.27% | 80.24% | +5.97 pts |
| SPF FAIL | 20.49% | 14.54% | −5.95 pts |
| DKIM PASS | 86.64% | 90.90% | +4.26 pts |
| DKIM FAIL | 3.27% | 1.67% | −1.60 pts |
SPF had the biggest single-year improvement of any protocol. A 5.97 point jump in twelve months is extraordinary for an infrastructure metric. For comparison, IPv6 adoption has moved less than 3 points in the same window. The explanation is almost certainly the Google and Yahoo bulk sender enforcement that went into full effect during 2024 and kept tightening through 2025. Companies that were previously "soft-compliant" had to properly publish and maintain their SPF records, or their marketing and transactional email stopped landing in inboxes.
Third-party crawl data tells the same story. Red Sift reported in early 2025 that 2.3 million organizations adopted DMARC over the previous twelve months, and that the adoption rate literally doubled after the Google and Yahoo mandate came into force. EasyDMARC's 2026 Adoption Report, which analyzed 1.8 million domains alongside the Fortune 500 and Inc. 5000, tells a similar story: adoption is up sharply, but enforcement is lagging behind. Proofpoint's telemetry, which covers 2.8 trillion scanned emails across 230,000 organizations, has independently flagged 2024 to 2025 as the fastest improvement in email authentication adoption it has ever measured.
DKIM's 4.26 point jump is also remarkable. DKIM is the harder protocol to get right. It requires generating keys, publishing them in DNS, and configuring your mail server to sign outbound messages. That 90.90% global pass rate means DKIM has effectively become the default for business email, not the exception. If your outbound mail isn't DKIM-signed in 2026, you are measurably out-of-step with the rest of the internet.
DMARC's 2.58 point jump is smaller than SPF's, but more significant. DMARC is the final layer. It only matters if SPF and DKIM are already in place. A DMARC pass rate of 88.99% means the vast majority of global email has all three protocols configured and aligned. If I had to pick a single proxy for "this organization has its email infrastructure sorted," DMARC pass rate is the one I'd use.
Why SPF failures still matter, even when DMARC passes
Here's the twist that deliverability engineers understand but most marketers don't: DMARC can pass even when SPF fails, as long as DKIM passes with alignment. So you might look at that 88.99% DMARC pass rate and assume SPF failures don't really matter.
They do. Here's why.
SPF failures are visible to receiving mail servers before DMARC evaluation happens. Many spam filters weight SPF failures heavily in their scoring models regardless of the DMARC outcome. A message that passes DMARC via DKIM but fails SPF is still more likely to land in the Promotions tab or the Junk folder than a message that passes both.
SPF failures are also the leading cause of "DMARC broke my mailing list" incidents. When an employee subscribes to a mailing list with their corporate address and the list forwards messages, the forwarded copy almost always fails SPF (because the list server isn't in the sender's SPF record). If DKIM is also broken by content modification, such as footer injection or Subject rewriting, both mechanisms fail and DMARC rejects the message. This is exactly why ARC exists. And exactly why the 70.07% of emails still missing an ARC header should worry anyone running a deliverability program.
There's a third reason to care about SPF. It correlates with organizational sophistication in a way that almost no other public signal does. A company with a clean, well-maintained SPF record, proper include: directives, and fewer than 10 DNS lookups is a company where IT, marketing, and security talk to each other. A company with ?all or a broken include: chain is a company where those teams don't coordinate.
I've seen hundreds of thousands of SPF records in the course of running TechnologyChecker's crawl pipeline, and one pattern repeats relentlessly. A company adopts a new sending platform (a fresh Marketo instance, a SendGrid account for transactional mail, you pick the example) and forgets to update its SPF include: directive. Nobody notices until campaign bounce rates spike two weeks later. By that point, 40,000 messages have already landed in junk folders. It's the single most common cause of "why did our open rate drop?" incidents I've watched unfold in customer data.
The encryption gap: 1 in 12 emails still flows in plaintext
Email authentication is only half the story. The other half is whether the message itself is encrypted in transit. We pulled the Cloudflare Email Routing encrypted-vs-plaintext data for Q1 2026:
| Status | Q1 2025 | Q1 2026 | YoY Delta |
|---|---|---|---|
| Encrypted | 89.67% | 91.79% | +2.12 pts |
| Not encrypted | 10.33% | 8.21% | −2.12 pts |
Progress is real. The encrypted share climbed more than 2 percentage points year-over-year. But the absolute number still matters: 1 in every 12 emails flowing through Cloudflare's network in Q1 2026 was not encrypted in transit. That means the message contents, the subject line, the sender, and every recipient address traveled between mail servers in plaintext, readable by anyone with access to the network path.
This isn't unique to Cloudflare. Google's own Email Encryption in Transit Transparency Report, which publishes aggregated data for mail flowing to and from Gmail, has shown a similar long tail of unencrypted traffic for years. Regional variation ranges from near-100% TLS for mail exchanged with major EU providers down to the 70s for some emerging markets. Two independent datasets (Cloudflare's Email Security and Google's Gmail transparency data) agreeing on roughly the same encryption ceiling is about as good as cross-validation gets in this kind of research.
In 2026. Nine years after Let's Encrypt made TLS certificates free and automatic.
If you work in healthcare, finance, or legal, an 8.21% plaintext rate isn't an abstract statistic. It's a compliance risk. Every one of those unencrypted messages is a potential reportable incident under HIPAA, PCI-DSS, or GDPR.
The TLS 1.0 scandal: Deprecated protocols are still carrying your email
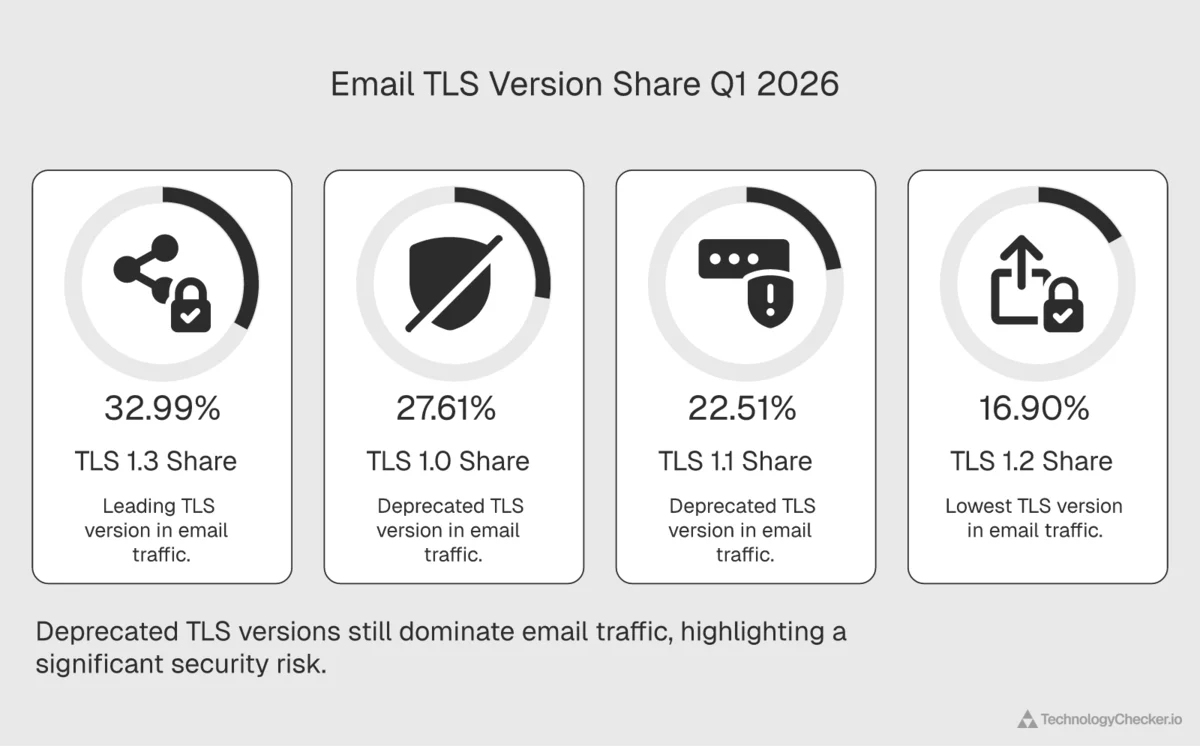
This was the most surprising finding in the entire Q1 2026 dataset, and it deserves its own section. We pulled the TLS version breakdown for all encrypted email traffic:
| TLS Version | Q1 2026 Share | IETF Status |
|---|---|---|
| TLS 1.0 | 27.61% | Deprecated March 2021 (RFC 8996) |
| TLS 1.1 | 22.51% | Deprecated March 2021 (RFC 8996) |
| TLS 1.2 | 16.90% | Still acceptable |
| TLS 1.3 | 32.99% | Modern, recommended |
Let me repeat that, because it took me two re-reads to believe it. 50.12% of encrypted email traffic in Q1 2026 is using a TLS version that was formally deprecated by the IETF in March 2021. Only 32.99% is using the modern TLS 1.3 standard, which has been around since 2018.
Some context for how strange that is. Most modern web browsers dropped TLS 1.0 and 1.1 support in 2020; if you try to visit a website using those protocols today, your browser will refuse. Major web hosts, CDNs, and API services rejected TLS 1.0 connections years ago. The PCI Security Standards Council officially prohibited TLS 1.0 for processing cardholder data on June 30, 2018, and PCI DSS has required a minimum of TLS 1.1 (TLS 1.2 strongly encouraged) for any in-scope system ever since. That was almost eight years ago.
Email is different. Because SMTP falls back to unencrypted transmission if TLS negotiation fails, mail servers have historically been reluctant to reject outdated TLS versions. The alternative is the email travels in plaintext instead. So the infrastructure silently accumulated a backlog of ancient TLS implementations nobody bothered to upgrade.
I've spent enough time in Edinburgh data centers staring at on-premises Exchange servers to know why this happens. Upgrading a mail relay isn't a weekend project. It's a political project. Some of these TLS 1.0 endpoints are running because a single downstream system (often a legacy ERP, a vendor integration, or an old scanning appliance that emails PDFs to a shared inbox) can't negotiate anything newer, and nobody wants to be the team that broke the chain to fix something that looks like it's "working fine." I've seen Fortune 500 companies push a TLS upgrade six or seven quarters in a row before it actually landed. I've seen mid-market companies solve the same problem in an afternoon. The deciding factor was rarely technical. It was almost always who had the authority to break things temporarily.
This is where email authentication maturity and email transport maturity part ways. A company can publish a p=reject DMARC record and simultaneously have an Exchange server still negotiating TLS 1.0 on port 25. The DMARC record signals sophistication. The TLS version reveals the truth.
The spoofing reality: 18.11% of inbound messages are fake

Cloudflare Radar's email security data also classifies inbound mail as either spoofed or legitimate. In Q1 2026, 18.11% of all inbound mail at Cloudflare-protected mailboxes was classified as a spoof attempt, with 81.89% as legitimate.
Roughly 1 in every 5.5 inbound emails. That number is a direct consequence of the authentication gaps we discussed earlier. Every domain without a DMARC p=reject policy is a potential impersonation target. Every fragile SPF record is an opening for a spoofer to craft a message that looks legitimate to a downstream spam filter.
The 88.99% DMARC pass rate we celebrated at the start of this post only applies to messages from domains that have DMARC configured. The 18.11% spoof rate is what happens in the gap, when attackers exploit the 6.68% of senders with no DMARC policy, or find a way around a misconfigured one.
The financial consequences of that gap aren't hypothetical. The FBI's 2024 Internet Crime Report (IC3), the most authoritative public dataset on cybercrime losses in the United States, reported $2.77 billion in Business Email Compromise losses across 21,442 incidents in 2024 alone. That makes BEC the second most profitable scam in cybercrime by reported losses. Total cybercrime losses reported to IC3 hit $16.6 billion in 2024, a 33% year-over-year increase.
The Verizon 2025 Data Breach Investigations Report puts the global BEC figure even higher, at $6.3 billion. Phishing appears in 57% of all social-engineering incidents, the median BEC loss sits at $50,000 per incident, and in 88% of confirmed BEC cases the payout was a wire transfer. In other words, the damage was typically irreversible by the time it was discovered.
Valimail, using its own monitoring network, tracked 2.53 billion suspicious emails on behalf of its customers during 2025. The company's 2026 State of DMARC Report, published February 12, 2026, explicitly ties the scale of those attacks to the enforcement gap: "most domains with DMARC are not fully protected," and attackers know it. Organizations that stop at p=none get all the mailbox-provider compliance benefits and none of the actual anti-spoofing protection.
When a prospect asks me how to quickly judge whether a supplier takes security seriously, I always give them the same advice. Check their DMARC policy, not their website copy. Not the ISO 27001 badge, not the compliance page, not the security.txt file. Pull up a terminal, run dig txt _dmarc.theirdomain.com, and read what comes back. If it's missing, or if the policy is p=none, you are looking at an organization whose security posture is mostly performance. It takes ten seconds, and it's the single most predictive public signal of whether they've actually thought about email spoofing as a real attack surface.
The ARC paradox: Why 70% of emails lose their authentication when forwarded
One last finding before we get to the implications. We pulled the ARC (Authenticated Received Chain) summary for Q1 2026:
| ARC Status | Share |
|---|---|
| NONE (no ARC header) | 70.07% |
| PASS | 29.25% |
| FAIL | 0.68% |
ARC is the protocol that lets mail forwarders, mailing lists, and intermediate relays preserve the original DMARC result even when they have to modify the message. Without ARC, a forwarded email has no reliable way to prove "this was authenticated when it originally entered the system."
70.07% of all email traffic has no ARC header. So when your email gets forwarded (by a mailing list, by a corporate mail relay, by a "forward to personal account" rule) the original authentication chain is typically lost, and the recipient's mail server has to make a best-guess call about whether to trust it.
Corporate email forwarding is a deliverability minefield for exactly this reason. It's also why your CEO's forwards@domain.com alias breaks every time marketing sends a campaign, and why the gap between authentication maturity and forwarding maturity is one of the clearest signals of how modern an email infrastructure actually is.
What email authentication maturity tells you about a company
Across the 50 million domains our crawlers scan every month, one pattern repeats: companies that get email authentication right almost always have modern technology stacks across the board.
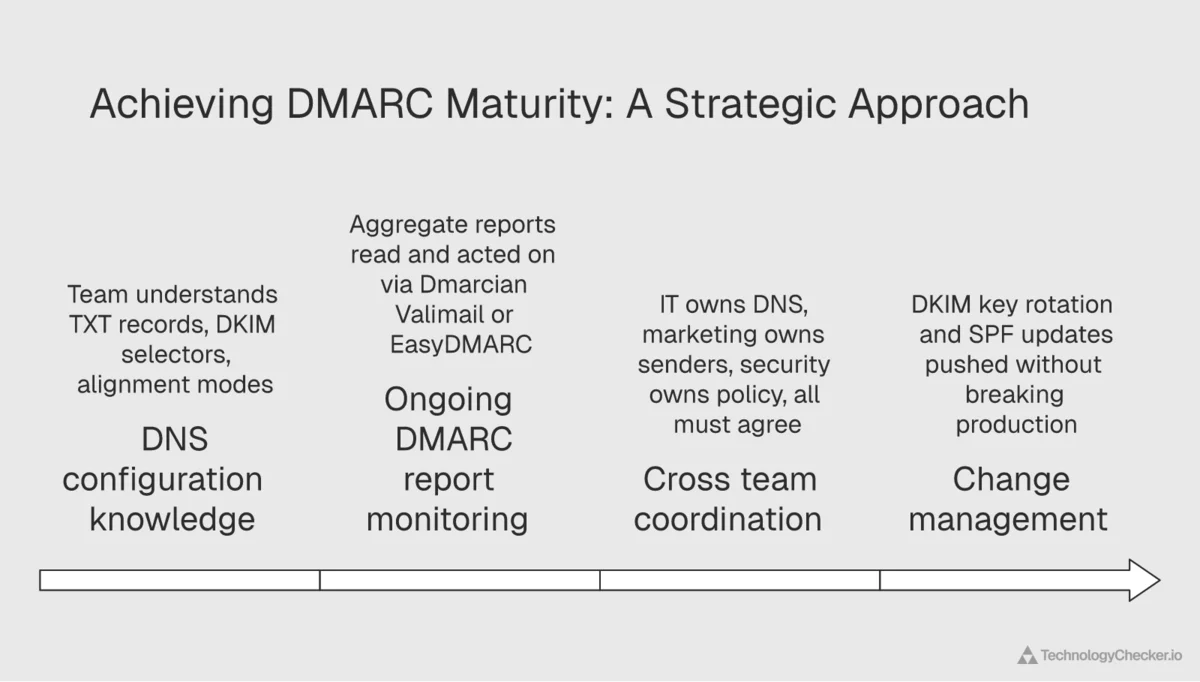
That isn't a coincidence. Getting DMARC right is mostly an organizational problem, not a technical one. Someone on the team needs to understand TXT records, DKIM selectors, and alignment modes. Someone has to actually read the DMARC aggregate reports that arrive at the rua= address every day, either by hand or through a platform like Dmarcian, Valimail, or EasyDMARC. IT owns the DNS, marketing owns the sending platforms (HubSpot, Marketo, Salesforce), security owns the policies, and all three teams have to agree on what the record says. And when someone rotates a DKIM key or adds a new sender to SPF, somebody else has to remember to update the DNS without breaking production.
Organizations that can pull all that off consistently also tend to have mature technology operations everywhere else. They run modern CRMs. They have real analytics infrastructure. They've built DevOps pipelines. They have the kind of internal alignment that lets them ship technology changes without breaking things.
Organizations that can't? They have v=spf1 ?all records, unsigned DKIM, no DMARC policy, and when we look at the rest of their stack, we usually find an outdated CRM, no marketing automation, and a website built on tech from five years ago.
Email authentication isn't the cause of technology sophistication. It's a symptom of it. But because the symptom is publicly visible in DNS and measurable at scale, it's one of the most reliable signals we've found.
What this means for B2B email outreach teams
If your team does outbound email (sales prospecting, marketing campaigns, account-based outreach) the Q1 2026 data has practical implications.
-
Assume your recipients are enforcing DMARC. With 88.99% global DMARC pass rates and Google and Yahoo both mandating compliance for bulk senders, treat strict DMARC enforcement as the default. Your own SPF, DKIM, and DMARC configuration has to be perfect. No
?allsoft-fails, no missing DKIM signatures, no mismatched alignment. -
Don't rely on SPF alone. The 14.54% global SPF failure rate tells you SPF is fragile. Every forwarding server, mailing list, or relay can break it. If you're not DKIM-signing every outbound message, you're one misconfigured relay away from your deliverability collapsing.
-
Audit your TLS versions. The 50% of email still using TLS 1.0 or 1.1 is both a risk and an opportunity. If your mail server is among them, upgrade now. Modern receiving infrastructure increasingly flags deprecated TLS as suspicious. If your recipients' servers are among them, assume message contents are more exposed than you think.
-
Use email authentication as a qualification signal. A prospect with no DMARC record, a broken SPF chain, or a mail server still accepting TLS 1.0 has immature infrastructure. That's a quality signal for your lead scoring. It's positive for some ICPs (teams selling email security solutions) and negative for others (teams selling enterprise software that needs technical maturity to implement).
-
Don't over-index on BIMI alone. Brand Indicators for Message Identification is the standard that puts your company logo next to authenticated messages in Gmail, Apple Mail, and Yahoo. It technically requires a DMARC policy at
p=quarantineorp=reject, which should make it a fantastic trust signal. The problem is scale. Valimail's 2026 report found BIMI adoption stalled at just 4% globally, meaning the vast majority of legitimately authenticated senders aren't even using it yet. Seeing a BIMI logo is a positive signal. Not seeing one tells you almost nothing. -
Don't forget the human element. The Verizon 2025 DBIR found that nearly 60% of breaches involve a human element (error, manipulation, or misuse). Perfect email authentication doesn't eliminate phishing. It just forces attackers into channels where the human on the keyboard is the final line of defense. That's why the most mature email security programs pair technical authentication (DMARC, SPF, DKIM, ARC) with phishing simulation training. Technology and awareness are complements, not substitutes.
From a single DMARC signal to a full technology profile
Email authentication maturity is one visible signal of how sophisticated a company's technology operations are. It's the tip of the iceberg. Companies that implement DMARC, SPF, and DKIM correctly almost always have modern marketing stacks (HubSpot, Marketo, Salesforce), real analytics infrastructure (Segment, Mixpanel), and mature DevOps practices.
That's the kind of correlated technology signal TechnologyChecker is built to detect. We monitor over 40,000 technologies across 50 million domains, and for every domain in the database we can tell you not just whether they have DMARC, but what's behind it. What marketing automation platform they use. What analytics stack runs on their website. What CRM sits behind their contact forms. What CDN fronts their application. Which authentication vendors they trust.
For sales teams, that means you can go beyond "does this company have DMARC?" to "what does their entire technology stack look like, and who's the decision-maker for each layer?" For marketing teams, your ideal customer profile can be a stack rather than a firmographic guess. For revenue operations, every prospect comes with a technographic fingerprint that explains which of your solutions will fit.
If you want to see the entire technology profile for any domain, you can start with a free lookup at TechnologyChecker.io.
A closing thought, from someone who has been reading DNS records at scale for the better part of a decade. Email authentication maturity is a bit like a good single malt. You can tell a surprising amount about the distillery from a single glass. You don't need to tour the whole operation to know whether they're cutting corners. A DMARC record with proper alignment, a clean SPF include: chain, DKIM signatures that actually verify, TLS 1.3 on the inbound MX. That combination is rare enough that when you see it, you know you're dealing with an engineering culture that takes the invisible stuff seriously. The invisible stuff is usually where the real quality hides.
Methodology and data sources
Primary (first-party) data
All percentages attributed to "Q1 2026" in this post are computed from Cloudflare Radar's email security dataset for the Q1 2026 period (January 1 through March 31, 2026). Year-over-year comparisons are pulled from the identical Q1 2025 window. The data reflects messages processed by Cloudflare Email Security, which handles a substantial share of global business email traffic, so the numbers are representative of real-world inbound mail rather than a sample of published DNS records.
Specific Cloudflare Radar dimensions used:
summary/dmarc,summary/spf,summary/dkim— global pass/fail/none distributionssummary/tlsVersion— encrypted transport version breakdownsummary/spoof,summary/arc— spoofing classification and ARC header presencesummary/encrypted(from Cloudflare Email Routing) — encrypted vs plaintext transit ratestimeseriesGroups/dmarc— 90-day daily trend data used for directional analysis
All percentages are rounded to two decimal places. "Deprecated" TLS versions refers to RFC 8996, which formally deprecated TLS 1.0 and 1.1 in March 2021.
Third-party sources cross-referenced in this analysis
- Valimail 2026 State of DMARC Report (published February 12, 2026): 78% awareness vs. 42% enforcement gap, 2.53B suspicious emails tracked in 2025, 4% BIMI adoption, industry enforcement ranges.
- Red Sift / EasyDMARC 2026 Adoption Report: 2.3 million organizations adopted DMARC year-over-year, 14.9% of 73.3M sampled domains at p=none minimum, 2.5% (~1.8M) at p=reject, regional enforcement rates.
- EasyDMARC 2026 DMARC Adoption & Enforcement Report: analysis of 1.8M domains alongside Fortune 500 and Inc. 5000.
- FBI 2024 Internet Crime Report (IC3): $2.77B in BEC losses across 21,442 incidents in 2024, $16.6B total cybercrime losses, 33% YoY increase.
- Verizon 2025 Data Breach Investigations Report (DBIR): $6.3B in BEC losses, $50K median, 88% wire transfer, 57% phishing in social engineering, 60% of breaches involve human element.
- Proofpoint 2024-2025 Email Threat Analysis: telemetry covering 2.8 trillion scanned emails across 230,000 organizations.
- Dmarcian: Understanding Gmail and Yahoo DMARC Requirements: timeline and scope of the October 2023 announcement and the February 2024 enforcement start.
- Google Email Encryption in Transit Transparency Report: corroborating public dataset on Gmail TLS encryption rates.
- PCI Security Standards Council: Migrating from SSL and Early TLS: June 30, 2018 deadline for TLS 1.0 deprecation under PCI DSS v3.2.
Want to see the full technology stack behind any company's email authentication setup? TechnologyChecker.io scans 50 million domains monthly and detects over 40,000 technologies, including which DMARC processors, email security vendors, CRM platforms, and marketing automation tools each company relies on. Start a free lookup to see a complete technographic profile.
David Thomson
CTO